200-301 Online Practice Questions and Answers
Questions 4
DRAG DROP
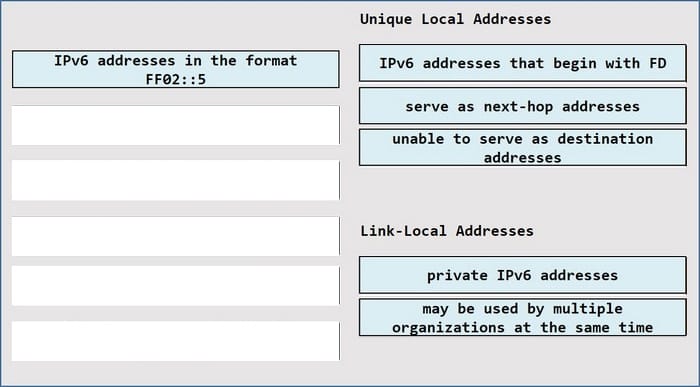
Drag and drop the IPv6 address types from the left onto their description on the right.
Select and Place:
Questions 5
What describes a northbound REST API for SDN?
A. network-element-facing interface for GET, POST, PUT, and DELETE methods
B. application-facing interface for SNMP GET requests
C. application-facing interface for GET, POST, PUT, and DELETE methods
D. network-element-facing interface for the control and data planes
Questions 6
Why implement VRRP?
A. to provide end users with a virtual gateway in a multivendor network
B. to leverage a weighting scheme to provide uninterrupted service
C. to detect link failures without the overhead of Bidirectional Forwarding Detection
D. to hand over to end users the autodiscovery of virtual gateways
Questions 7
What is a practice that protects a network from VLAN hopping attacks?
A. Enable dynamic ARP inspection
B. Configure an ACL to prevent traffic from changing VLANs
C. Change native VLAN to an unused VLAN ID
D. Implement port security on internet-facing VLANs
Questions 8
What is an appropriate use for private IPv4 addressing?
A. on the public-facing interface of a firewall
B. to allow hosts inside to communicate in both directions with hosts outside the organization
C. on internal hosts that stream data solely to external resources
D. on hosts that communicates only with other internal hosts
Questions 9
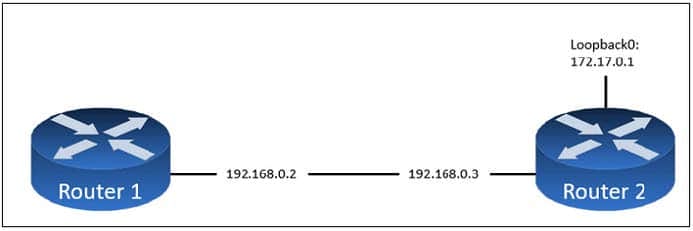
A. Router2(config)#ntp passive
B. Router2(config)#ntp server 172.17.0.1
C. Router2(config)#ntp master 4
D. Router2(config)#ntp server 192.168.0.2
Questions 10
Which two types of attack are categorized as social engineering? (Choose two.)
A. phoning
B. malvertising
C. probing
D. pharming
E. phishing
Questions 11
Refer to the exhibit. An administrator configures four switches for local authentication using passwords that are stored as a cryptographic hash. The four switches must also support SSH access for administrators to manage the network infrastructure. Which switch is configured correctly to meet these requirements?
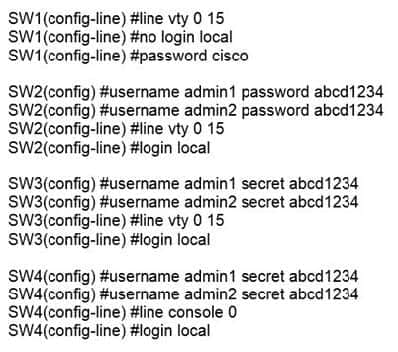
A. SW1
B. SW2
C. SW3
D. SW4
Questions 12
Which technology must be implemented to configure network device monitoring with the highest security?
A. IP SLA
B. syslog
C. NetFlow
D. SNMPv3
Questions 13
Which result occurs when PortFast is enabled on an interface that is connected to another switch?
A. Root port choice and spanning tree recalculation are accelerated when a switch link goes down.
B. After spanning tree converges, PortFast shuts down any port that receives BPDUs.
C. VTP is allowed to propagate VLAN configuration information from switch to switch automatically.
D. Spanning tree may fail to detect a switching loop in the network that causes broadcast storms.