Cisco Cybersecurity Operations: 210-255
Want to pass your Cisco Cybersecurity Operations 210-255 exam in the very first attempt? Try Pass2lead! It is equally effective for both starters and IT professionals.
- Vendor: Cisco
- Exam Code: 210-255
- Exam Name: Cisco Cybersecurity Operations
- Certifications: Cisco Certified CyberOps Associate
- Total Questions: 224 Q&As
- Updated on: Nov 03, 2022
- Exam retired ,new exam code replace: 200-201

- Q&As Identical to the VCE Product
- Windows, Mac, Linux, Mobile Phone
- Printable PDF without Watermark
- Instant Download Access
- Download Free PDF Demo
- Includes 365 Days of Free Updates
VCE
- Q&As Identical to the PDF Product
- Windows Only
- Simulates a Real Exam Environment
- Review Test History and Performance
- Instant Download Access
- Includes 365 Days of Free Updates
Passing Certification Exams Made Easy
Everything you need prepare and quickly pass the tough certification exams the first time
- 99.5% pass rate
- 7 Years experience
- 7000+ IT Exam Q&As
- 70000+ satisfied customers
- 365 days Free Update
- 3 days of preparation before your test
- 100% Safe shopping experience
- 24/7 Support
Free 210-255 Exam Questions in PDF Format
Related Cisco Certified CyberOps Associate Exams
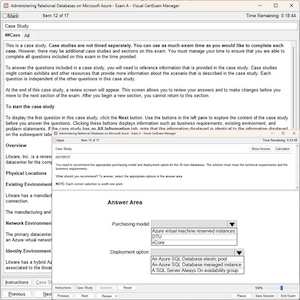
210-255 Online Practice Questions and Answers
Questions 1
Which process is being utilized when IPS events are removed to improve data integrity?
A. data normalization
B. data availability
C. data protection
D. data signature
Questions 2
Refer to the exhibit. Which type of log is this an example of?
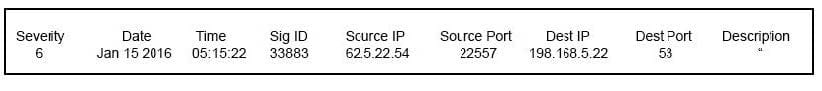
A. IDS log
B. proxy log
C. NetFlow log
D. syslog
Questions 3
Which of the following file systems is more secure, scalable, and advanced?
A. FAT32
B. FAT64
C. uFAT
D. NTFS
Reviews
-
I love this dumps. It really helpful and convenient. Recommend strongly.
-
Pass with score 964/1000, this dumps is valid. I think this dumps is enough for the exam, so you can trust on it.
-
hi guys this dumps is enough to pass the exam because i have passed the exam just with the help of this dumps, so you can do it.
-
i cannot image that i would pass the exam with so high score, thanks for this dumps. Recommend.
-
Absolutely valid. i passed today. You are the best. Thanks so much.
-
This is the valid dumps. I passed mine yesterday. All the questions are from this dumps. Thanks.
-
Now, i have finished my exam. I really appreciate for the help of this dumps. Thanks very much.
-
Many questions are from the dumps but few question changed. Need to be attention.
-
Test engine works fine. Pass my exam. Thank you.
-
I have met the same question like this material in the exam. I haven't notice any new question. Thanks. Good luck to all!

 Printable PDF
Printable PDF