156-215.81 Online Practice Questions and Answers
Questions 4
John is using Management HA. Which Smartcenter should be connected to for making changes?
A. secondary Smartcenter
B. active Smartcenter
C. connect virtual IP of Smartcenter HA
D. primary Smartcenter
Questions 5
In which scenario is it a valid option to transfer a license from one hardware device to another?
A. From a 4400 Appliance to an HP Open Server
B. From an IBM Open Server to an HP Open Server
C. From an 4400 Appliance to a 2200 Appliance
D. From an IBM Open Server to a 2200 Appliance
Questions 6
Which feature in R77 permits blocking specific IP addresses for a specified time period?
A. Suspicious Activity Monitoring
B. HTTP Methods
C. Local Interface Spoofing
D. Block Port Overflow
Questions 7
Your boss wants you to closely monitor an employee suspected of transferring company secrets to the competition. The IT department discovered the suspect installed a WinSCP client in order to use encrypted communication. Which of the following methods is BEST to accomplish this task?
A. Use SmartView Tracker to follow his actions by filtering log entries that feature the WinSCP destination port. Then, export the corresponding entries to a separate log file for documentation.
B. Use SmartDashboard to add a rule in the firewall Rule Base that matches his IP address, and those of potential targets and suspicious protocols. Apply the alert action or customized messaging.
C. Watch his IP in SmartView Monitor by setting an alert action to any packet that matches your Rule Base and his IP address for inbound and outbound traffic.
D. Send the suspect an email with a keylogging Trojan attached, to get direct information about his wrongdoings.
Questions 8
VPN gateways must authenticate to each other prior to exchanging information. What are the two types of credentials used for authentication?
A. 3DES and MD5
B. Certificates and IPsec
C. Certificates and pre-shared secret
D. IPsec and VPN Domains
Questions 9
The system administrator of a company is trying to find out why acceleration is not working for the traffic. The traffic is allowed according to the rule base and checked for viruses. But it is not accelerated. What is the most likely reason that the traffic is not accelerated?
A. There is a virus found. Traffic is still allowed but not accelerated
B. The connection required a Security server
C. Acceleration is not enabled
D. The traffic is originating from the gateway itself
Questions 10
Which VPN routing option uses VPN routing for every connection a satellite gateway handles?
A. To satellites through center only
B. To center only
C. To center and to other satellites through center
D. To center, or through the center to other satellites, to internet and other VPN targets
Questions 11
What does it mean if Bob gets this result on an object search? Refer to the image below. Choose the BEST answer.
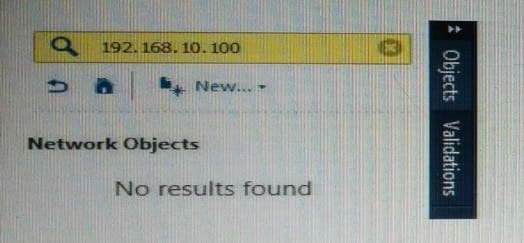
A. Search detailed is missing the subnet mask.
B. There is no object on the database with that name or that IP address.
C. There is no object on the database with that IP address.
D. Object does not have a NAT IP address.
Questions 12
In ____________ NAT, the ____________ is translated.
A. Hide; source
B. Static; source
C. Simple; source
D. Hide; destination
Questions 13
Which software blade does NOT accompany the Threat Prevention policy?
A. Anti-virus
B. IPS
C. Threat Emulation
D. Application Control and URL Filtering
