1Z0-1104-22 Online Practice Questions and Answers
Questions 4
Which statement is true about Oracle Cloud Infrastructure (OCI) Object Storage server-side encryption?
A. All the traffic to and from object storage is encrypted by using Transport Layer Security.
B. Encryption is not enabled by default.
C. Customer-provided encryption keys are never stored in OCI Vault service.
D. Each object in a bucket is always encrypted with the same data encryption key.
Questions 5
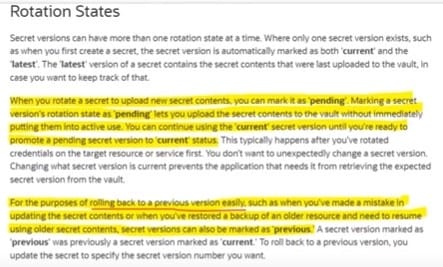
Operations team has made a mistake in updating the secret contents and immediately need to resume usingolder secret contents in OCI Secret Management within a Vault. As a Security Administrator, what step should you perform to rollback to last version? Select TWO correct answers.
A. Mark the secret version as 'deprecated'
B. Mark the secret version as'Previous'
C. Mark the secret version as 'Rewind'
D. Upload new secret and mark as 'Pending'. Promote this secret version as 'Current'
Questions 6
Which statement is true about origin management in WAF?
Statement A: Multiple origins can be defined.
Statement B: Only a single origin can be active fora WAF.
A. Only statement B is true.
B. Both the statements are false.
C. Both the statements are true.
D. Only statement A is true.
Questions 7
Which challenge is generally the first level of bot mitigation, but not sufficient with more advanced bot tools?
A. CAPTCHA challenge
B. JavaScript challenge
C. Device fingerprint challenge
D. Human interaction challenge
Questions 8
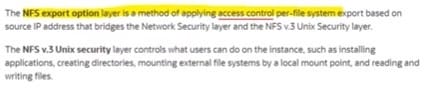
A company has OCI tenancy which has mount target associated with two File Systems, CG_1 and CG_2. These FileSystems are accessed by IP-based clients AB_1 and AB_2 respectively. As a security administrator, how can you provide access to both clients such that CGI has Read only access on AB1 and CG_2 has Read/Write access on AB_2?
A. NFS Export Option
B. Access Control Lists
C. NFS v3 Unix Security
D. Vault
Questions 9
On which option do you set Oracle Cloud Infrastructure Budget?
A. Compartments
B. Instances
C. Free-form tags
D. Tenancy
Questions 10
Which statement is trueabout standards?
A. They may be audited.
B. They are result of a regulation or contractual requirement or an industry requirement.
C. They are methods and instructions on how to maintain or accomplish the directives of the policy.
D. They are the foundation of corporate governance.
Questions 11
What would you use to make Oracle Cloud Infrastructure Identity and Access Management govern resources in a tenancy?
A. Policies
B. Users
C. Dynamic groups
D. Groups
Questions 12
A number ofmalicious requests for a web application is coming from a set of IP addresses originating from Antartica.
Which of the following statement will help to reduce these types of unauthorized requests ?
A. Delete NAT Gateway from Virtual Cloud Network
B. Use WAF policy using Access Control Rules
C. List specific set of IP addresses then deny rules in Virtual Cloud Network Security Lists
D. Change your home region in which your resources are currently deployed
Questions 13
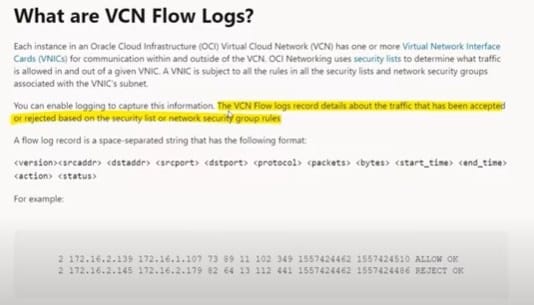
VCN Flow log record details about the traffic that has been denied or approved is based on which of the following statements?
A. Configuration of route table
B. Security Lists orNetwork Security Group Rules
C. Web Application Firewall (WAF)
D. Auth tokens