1Z0-160 Online Practice Questions and Answers
Questions 4
Which two situations require that your Database Deployment be scaled up?
A. The Database Deployment instance is maxed out on semaphore sets.
B. The database instance has reached the limit in the license_max_sessionsdatabase parameter.
C. The Database Deployment is maxed out on CPU.
D. The database instance is out of space in the sysaux and system tablespaces.
E. The Database Deployment is maxed out on storage.
F. The Database Deployment is maxed out on semaphores.
Questions 5
How would you connect from your local machine to the database instance on a Database Deployment by using SQL*Net?
A. You start an SSH process on your local machine to communicate to a tunnel created on the Database Deployment compute node.
B. You must use port 1521 and the TCP/IP SSL communication protocol.
C. You can use only the SSH connection that is defined on port 22 that is configured by default during Database Deployment installation.
D. You use Transparent Data Encryption (TDE) to secure connections to the database instance on the Database Deployment.
Questions 6
You are on the Database Cloud Service Instance View page.
Which three consoles can you open?
A. OPC Console
B. GlassFish Administration Console
C. Storage Container Console
D. Application Express Console
E. User Console
F. Database Express Manager Console
Questions 7
A key pair is required to create a Database Deployment.
What can the key pair be used for?
A. They key pair is used to start up, shut down, and manage EM Express availability.
B. The keys are used to control the encryption that is used by Database Deployment: the first is for network encryption and the second is for database encryption.
C. The keys replace password use. Database Deployment use only key pairs; password authentication is not enable for SSH default connections.
D. Communication between instances in a Database Cloud Service account is controlled by network security rules and security lists.
Questions 8
You want to perform an on-demand backup.
Which two statements are true?
A. Connect to the instance's VM as the opc user.
B. Connect to the instance's VM as the oracle user.
C. Disable the backup configuration (crontab).
D. Enable the backup configuration (crontab).
Questions 9
Which two statements are true about the Database Deployments and Oracle database instances that are provided by Oracle Public Cloud?
A. A Database Deployment Virtual Image always provides a pre-created Oracle database.
B. An Oracle database instance that is provided as part of Oracle Database Cloud Service runs a different executable than would be run with the same version and release of Oracle Database on private premises.
C. A Database Deployment Virtual Image always provides a Linux virtual machine.
D. A Database Deployment Virtual Image requires customers to install their preferred version on the Oracle database software.
E. Multiple Oracle database instances can run in a Database Deployment on Oracle Public Cloud.
Questions 10
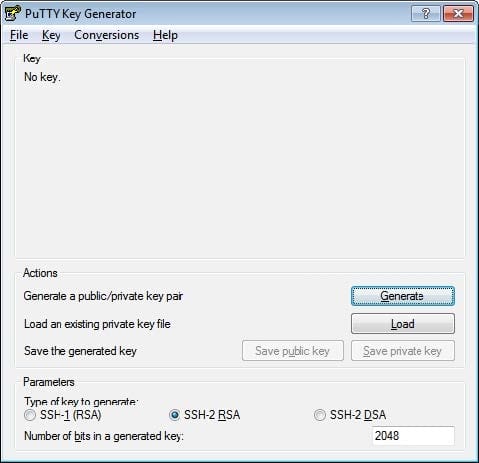
Which three statements are true about SSH tunnels in an Oracle Database Cloud Service configuration?
A. A separate SSH tunnel is required for each port that is required for the environment.
B. The SSH tunnel should include all required ports for the environment.
C. The available protocols include ssh-2 DSA.
D. The default protocol is ssh-1 RSA.
E. The SSH tunnel is opened automatically by the Cloud Services VPN and remains open.
F. The SSH tunnel must be opened manually and must remain open.
Questions 11
You created a Database Deployment and predefined security rules were generated.
Which two predefined security rules were generated when you created the Database Deployment?
A. The ora_p2_ssh security rule for the public-internet security IP list was created to communicate with the ora_dbpredefined network group over SSH.
B. The ora_db_public security rules to manage database access through the default port 1521 and the ora_db_admin security rules for SSH connection via SQL*Net through port 5500 were created.
C. The ora_access db security rule for SSH connection via PuTTY is created to configure network rules and ora_access_consolefor HTTPS access to Oracle Cloud Services Console.
D. No security rules are created by default and users must manually configure all access rules.
E. The ora_p2_dblistener security rule for the public-internet security IP list (any host on the Internet) was created to communicate with the ora_dbpredefined network group over SQL*Net.
Questions 12
Which two statements are true about the SSH tunnels within an Oracle Database Cloud Service environment?
A. An individual SSH tunnel is required for each port in the environment.
B. The client must provide the server with the SSH private key.
C. The SSH tunnel must be selected by a security rule to enable remote access.
D. The server must hold the SSH public and private keys in the SSH authorized_keysfile.
E. Oracle Database Cloud Service provides a centralized key server for all SSH connections.
Questions 13
What would be the number of bits in the SSH key generated by using the ssh-keygen tool, which is used to connect to Oracle Cloud?
A. 4096
B. 1024
C. 2048
D. 512