200-201 Online Practice Questions and Answers
Questions 4
Which security model assumes an attacker within and outside of the network and enforces strict verification before connecting to any system or resource within the organization?
A. Biba
B. Object-capability
C. Take-Grant
D. Zero Trust
Questions 5
Syslog collecting software is installed on the server For the log containment, a disk with FAT type partition is used An engineer determined that log files are being corrupted when the 4 GB tile size is exceeded. Which action resolves the issue?
A. Add space to the existing partition and lower the retention penod.
B. Use FAT32 to exceed the limit of 4 GB.
C. Use the Ext4 partition because it can hold files up to 16 TB.
D. Use NTFS partition for log file containment
Questions 6
Refer to the exhibit.
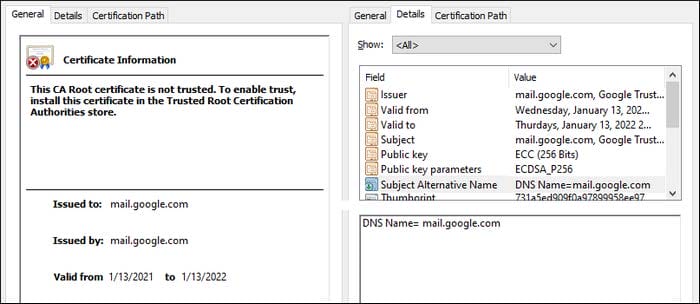
A company employee is connecting to mail google.com from an endpoint device. The website is loaded but with an error. What is occurring?
A. DNS hijacking attack
B. Endpoint local time is invalid.
C. Certificate is not in trusted roots.
D. man-m-the-middle attack
Questions 7
Which process represents the application-level allow list?
A. allowing everything and denying specific executable files
B. allowing everything and denying specific applications protocols
C. allowing specific files and deny everything else
D. allowing specific format files and deny executable files
Questions 8
Refer to the exhibit.
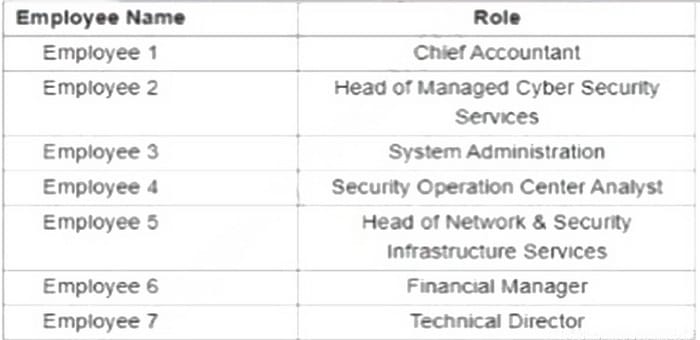
A suspicious IP address is tagged by Threat Intelligence as a brute-force attempt source. After the attacker produces many of failed login entries it successfully compromises the account. Which stakeholder is responsible for the incident response detection step?
A. employee 2
B. employee 3
C. employee 4
D. employee 5
Questions 9
What is the role of NAT in data visibility?
A. load balancing
B. hiding IP addresses
C. web filtering
D. encrypting files
Questions 10
What are two denial-of-service (DoS) attacks? (Choose two)
A. port scan
B. SYN flood
C. man-in-the-middle
D. phishing
E. teardrop
Questions 11
Which security monitoring data type requires the largest storage space?
A. transaction data
B. statistical data
C. session data
D. full packet capture
Questions 12
Refer to the exhibit.
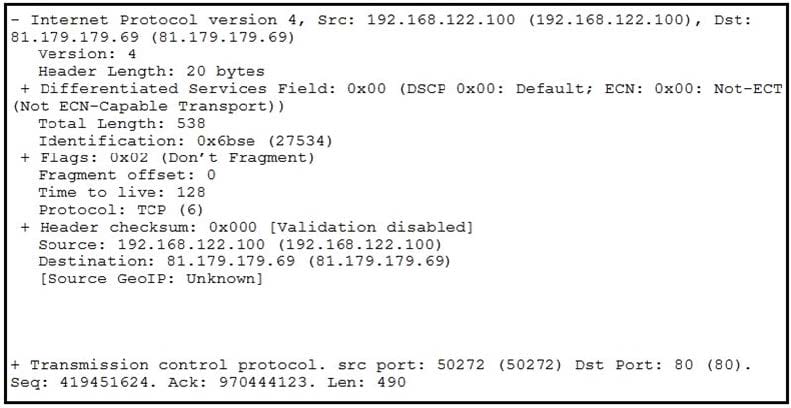
What should be interpreted from this packet capture?
A. 81.179.179.69 is sending a packet from port 80 to port 50272 of IP address 192.168.122.100 using UDP protocol.
B. 192.168.122.100 is sending a packet from port 50272 to port 80 of IP address 81.179.179.69 using TCP protocol.
C. 192.168.122.100 is sending a packet from port 80 to port 50272 of IP address 81.179.179.69 using UDP protocol.
D. 81.179.179.69 is sending a packet from port 50272 to port 80 of IP address 192.168.122.100 using TCP UDP protocol.
Questions 13
During which phase of the forensic process are tools and techniques used to extract information from the collected data?
A. investigation
B. examination
C. reporting
D. collection
