300-625 Online Practice Questions and Answers
Questions 4
Which two steps are mutual between Cisco secure boot and UEFI secure boot? (Choose two.)
A. bootloader
B. operating system
C. microloader
D. kemel
E. hardware anchor
Questions 5
Which Cisco NX-OS command displays the VSAN that is associated with each FCID?
A. show fcdomain
B. show fc2 plogi
C. show vsan database
D. show flogi database
Questions 6
A storage administrator wants to enable NPV in a Fibre Channel edge switch. Which configuration is supported in this mode?
A. Cisco Fabric Services distribution over Fibre Channel
B. E Port connectivity to the core switch
C. local switching of east-west traffic
D. Dynamic Port VSAN Membership
Questions 7
A storage network engineer must install and configure a new MDS switch in a data center network. Which two statements about available choices during the MDS switch initial setup are correct? (Choose two.)
A. The engineer can choose what will be the administrator account.
B. The secure password standard is required.
C. The engineer can configure the default zone policy.
D. The engineer can configure the default switch port trunk mode.
E. The engineer does not have the choice to enable or disable full zoneset distribution.
Questions 8
Refer to the exhibit.
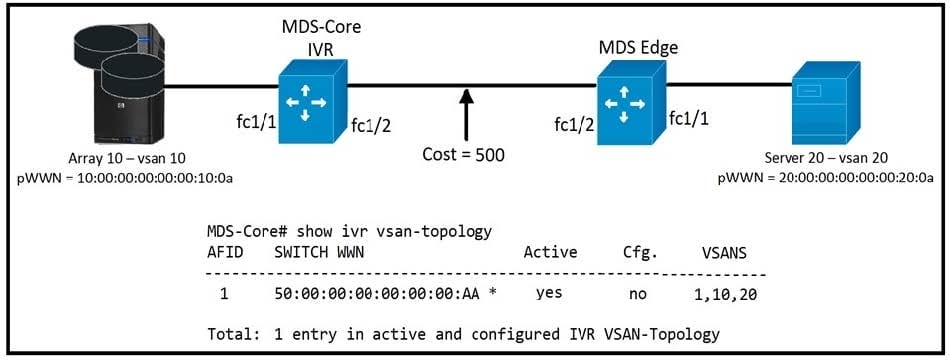
An engineer is configuring Inter-VSAN routing for two Cisco MDS switches. The FSPF cost between the switches is 500, and the Cisco MDS core virtualizes an IVR NAT domain as shown. Which statement about the topology is correct?
A. The MDS-Core simulates an IVR NAT, and the FSPF cost is 500.
B. The MDS-Core simulates an IVR NAT, and increases the cost to 501.
C. The MDS-Core simulates an IVR NAT, and decreases the cost to 400.
D. The MDS-Core simulates an IVR NAT, and increases the cost to 600.
Questions 9
Which action must be performed to deactivate a VSAN without losing its configuration?
A. Isolate it.
B. Delete it.
C. Rename it.
D. Suspend it.
Questions 10
Refer to the exhibit.
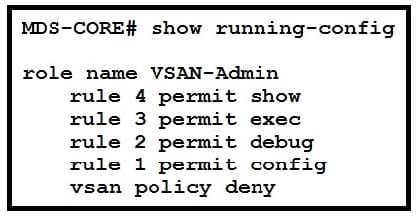
A network engineer created a new user that uses the VSAN-Admin role on a Cisco MDS switch so a new colleague can manage the VSANs configured on the switch. Which action is required for the configuration to give permission to the new colleague?
A. permit vsan 1-1000 must be configured as rule 5.
B. permit vsan 1-1000 must be configured as rule 1.
C. permit vsan 1-1000 must be configured under the VSAN policy deny.
D. permit vsan 1-1000 must be configured under the VSAN policy allow.
Questions 11
Refer to the exhibit.
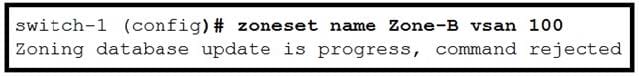
Which command is used to determine which switch has the lock?
A. show fcs ie vsan
B. show zoneset active
C. show zone status
D. show flogi database
Questions 12
Refer to the exhibits.
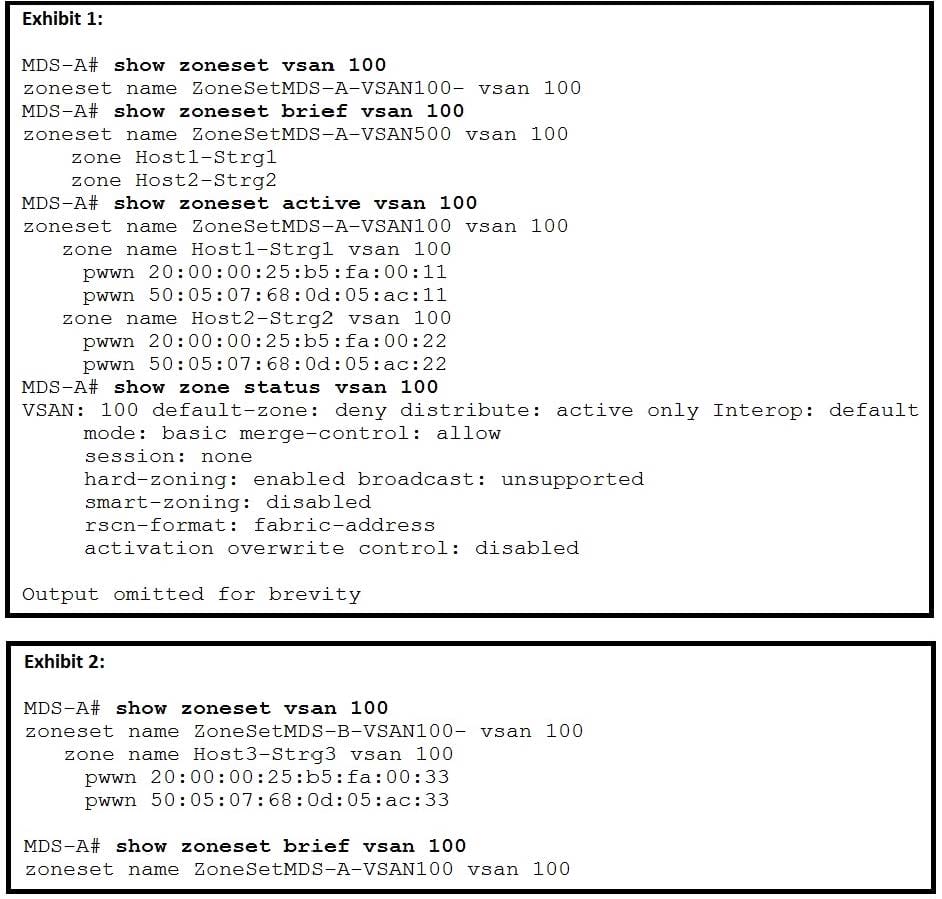
A storage network engineer activates a zoneset on MDS-A and verifies the successful activation (Exhibit 1). The engineer is then notified that there is a SAN outage (Exhibit 2) What is the cause of the outage?
A. Another network engineer activated zoneset ZoneSetMDS-B-VSAN100 on MDS-A.
B. Another network engineer issued the zone mode enhanced vsan 100 command on another switch in the fabric.
C. Another network engineer activated the zoneset ZoneSetMDS-B-VSAN100 command on another switch in the fabric.
D. Another network engineer issued the zone default-zone permit vsan 100 command on another switch in the fabric.
Questions 13
After a subordinate switch requests a domain ID form a principal switch, the requested domain ID becomes the runtime domain ID, and all interfaces on the affected VSAN are isolated. What is a solution to the issue?
A. Add the received ID to the allowed list.
B. Configure a static domain on the subordinate switch and reboot the switch.
C. Enable the FICON feature on the affected VSAN.
D. Configure IVR NAT on the affected VSAN.
