300-715 Online Practice Questions and Answers
Questions 4
Which default endpoint identity group does an endpoint that does not match any profile in Cisco ISE become a member of?
A. Endpoint
B. unknown
C. blacklist
D. white list
E. profiled
Questions 5
A user reports that a switch's RADIUS accounting packets are not being seen on the Cisco ISE server Which command is the user missing in the switch's configuration?
A. radius-server vsa send accounting
B. aaa accounting network default start-stop group radius
C. aaa accounting resource default start-stop group radius
D. aaa accounting exec default start-stop group radius
Questions 6
An engineer is migrating users from MAB to 802.1X on the network. This must be done during normal business hours with minimal impact to users. Which CoA method should be used?
A. Port Bounce
B. Port Shutdown
C. Session Termination
D. Session Reauthentication
Questions 7
There are several devices on a network that are considered critical and need to be placed into the ISE database and a policy used for them. The organization does not want to use profiling. What must be done to accomplish this goal?
A. Enter the MAC address in the correct Endpoint Identity Group.
B. Enter the MAC address in the correct Logical Profile.
C. Enter the IP address in the correct Logical Profile.
D. Enter the IP address in the correct Endpoint Identity Group.
Questions 8
Refer to the exhibit.
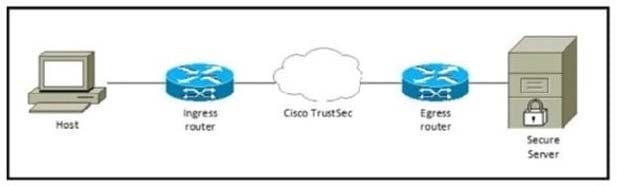
Which component must be configured to apply the SGACL?
A. egress router
B. host
C. secure server
D. ingress router
Questions 9
An administrator is configuring a new profiling policy in Cisco ISE for a printer type that is missing from the profiler feed The logical profile Printers must be used in the authorization rule and the rule must be hit.
What must be done to ensure that this configuration will be successful?
A. Create a new logical profile for the new printer policy
B. Enable the EndPoints:EndPointPolicy condition in the authorization policy.
C. Add the new profiling policy to the logical profile Printers.
D. Modify the profiler conditions to ensure that it goes into the correct logical profile
Questions 10
An administrator replaced a PSN in the distributed Cisco ISE environment. When endpoints authenticate to it, the devices are not getting the right profiles or attributes and as a result, are not hitting the correct policies. This was working correctly on the previous PSN. Which action must be taken to ensure the endpoints get identified?
A. Verify that the MnT node is tracking the session.
B. Verify the shared secret used between the switch and the PSN.
C. Verify that the profiling service is running on the new PSN.
D. Verify that the authentication request the PSN is receiving is not malformed.
Questions 11
The IT manager wants to provide different levels of access to network devices when users authenticate using TACACS+. The company needs specific commands to be allowed based on the Active Directory group membership of the different roles within the IT department. The solution must minimize the number of objects created in Cisco ISE. What must be created to accomplish this task?
A. one shell profile and one command set
B. multiple shell profiles and one command set
C. one shell profile and multiple command sets
D. multiple shell profiles and multiple command sets
Questions 12
An administrator must enable scanning for specific endpoints when they attempt to access the network. The scanning must be triggered as a result of successful authentication. Which action accomplishes this task?
A. Modify the authorization policy to send init_endpoint_scan as a result to the authenticator.
B. Create an authorization profile with scanning enabled and add it to the authorization policy that the endpoints will hit.
C. Add an entry in the authentication conditions to allow only scanned endpoints access, then redirect everything else to the portal to initiate the scan.
D. Configure the endpoint scanning probe to profile the endpoint correctly and assign it a risk score.
Questions 13
An administrator has manually added the MAC address of a wireless device to the Blocklist Identity Group for testing. When the device connects to the wireless network it triggers the Wireless Block List Default rule, but the device is still allowed to access the wireless network. What additional step must be taken to resolve tissue?
A. Disable URL redirection on the Authorization Profile.
B. Enable SNMP with read and write access on the Cisco WLC.
C. Create an ACL named BLOCKHOLE on the Cisco WLC.
D. Change the Access Type under the Authorization Profile lo ACCESS_REJECT.
