350-701 Online Practice Questions and Answers
Questions 4
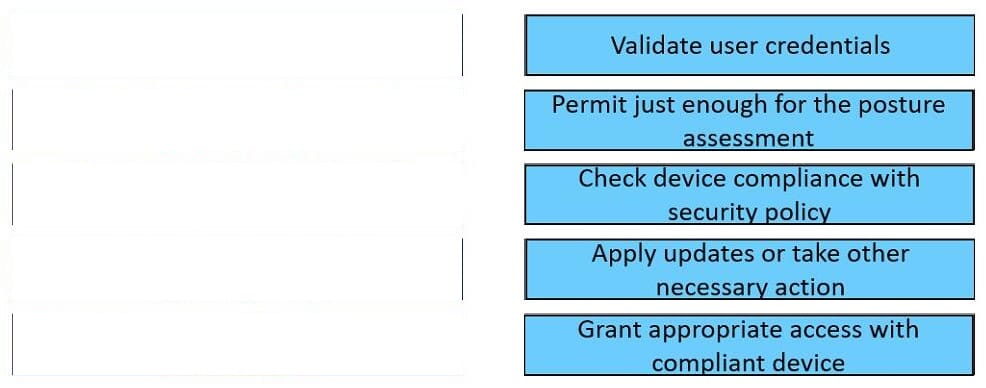
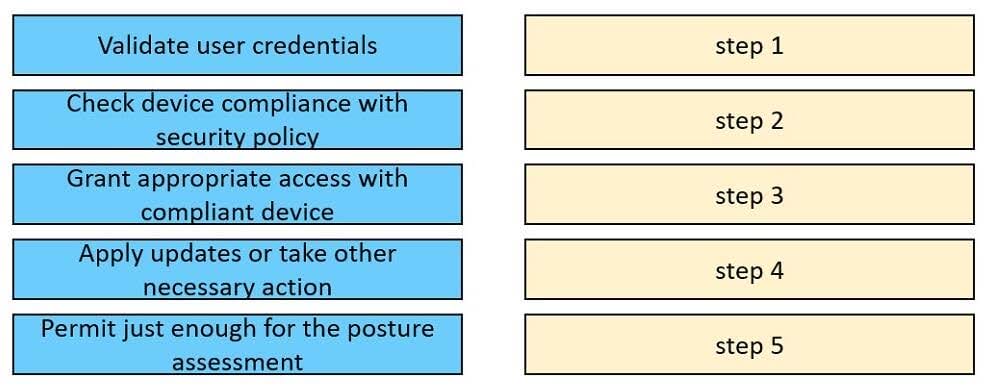
DRAG DROP
Drag and drop the posture assessment flow actions from the left into a sequence on the right.
Select and Place:
Questions 5
Which two features are used to configure Cisco ESA with a multilayer approach to fight viruses and malware? (Choose two)
A. Sophos engine
B. white list
C. RAT
D. outbreak filters
E. DLP
Questions 6
Which compliance status is shown when a configured posture policy requirement is not met?
A. compliant
B. unknown
C. authorized
D. noncompliant
Questions 7
Client workstations are experiencing extremely poor response time. An engineer suspects that an attacker is eavesdropping and making independent connections while relaying messages between victims to make them think they are talking to each other over a private connection. Which feature must be enabled and configured to provide relief from this type of attack?
A. Link Aggregation
B. Reverse ARP
C. private VLANs
D. Dynamic ARP Inspection
Questions 8
Which two Cisco ISE components enforce security policies on noncompliant endpoints by blocking network access? (Choose two.)
A. Apex licensing
B. TACACS+
C. profiling
D. DHCP and SNMP probes
E. posture agents
Questions 9
A network engineer must monitor user and device behavior within the on-premises network. This data must be sent to the Cisco Stealthwatch Cloud analytics platform for analysis. What must be done to meet this requirement using the Ubuntu-based VM appliance deployed in a VMware-based hypervisor?
A. Configure a Cisco FMC to send syslogs to Cisco Stealthwatch Cloud
B. Deploy the Cisco Stealthwatch Cloud PNM sensor that sends data to Cisco Stealthwatch Cloud
C. Deploy a Cisco FTD sensor to send network events to Cisco Stealthwatch Cloud
D. Configure a Cisco FMC to send NetFlow to Cisco Stealthwatch Cloud
Questions 10
When a next-generation endpoint security solution is selected for a company, what are two key deliverables that help justify the implementation? (Choose two.)
A. signature-based endpoint protection on company endpoints
B. macro-based protection to keep connected endpoints safe
C. continuous monitoring of all files that are located on connected endpoints
D. email integration to protect endpoints from malicious content that is located in email
E. real-time feeds from global threat intelligence centers
Questions 11
A Cisco ISE engineer configures Central Web Authentication (CWA) for wireless guest access and must have the guest endpoints redirect to the guest portal for authentication and authorization. While testing the policy, the engineer notices that the device is not redirected and instead gets full guest access. What must be done for the redirect to work?
A. Tag the guest portal in the CWA part of the Common Tasks section of the authorization profile for the authorization policy line that the unauthenticated devices hit.
B. Use the track movement option within the authorization profile for the authorization policy line that the unauthenticated devices hit.
C. Create an advanced attribute setting of Cisco:cisco-gateway-id=guest within the authorization profile for the authorization policy line that the unauthenticated devices hit.
D. Add the DACL name for the Airespace ACL configured on the WLC in the Common Tasks section of the authorization profile for the authorization policy line that the unauthenticated devices hit.
Questions 12
What is the function of SDN southbound API protocols?
A. to allow for the dynamic configuration of control plane applications
B. to enable the controller to make changes
C. to enable the controller to use REST
D. to allow for the static configuration of control plane applications
Questions 13
Which risk is created when using an Internet browser to access cloud-based service?
A. misconfiguration of infrastructure, which allows unauthorized access
B. intermittent connection to the cloud connectors
C. vulnerabilities within protocol
D. insecure implementation of API