C_AUDSEC_731 Online Practice Questions and Answers
Questions 4
You have to analyze risk and perform remediation to enable end-to-end compliance.
What is the correct sequence of steps?
A. 1. Identify and select risks to manage.
2.
Build and maintain rules.
3.
Detect authorization risk.
4.
Test and report the risk.
5.
Remediate and mitigate risk.
6.
Prevent the risk.
B. 1. Identify and select risks to manage.
2.
Build and maintain rules.
3.
Remediate and mitigate risk.
4.
Test and report the risk.
5.
Detect authorization risk.
6.
Prevent the risk.
C. 1. Identify and select risks to manage.
2.
Build and maintain rules.
3.
Detect authorization risk.
4.
Remediate and mitigate risk.
5.
Test and report the risk.
6.
Prevent the risk.
D. 1. Identify and select risks to manage.
2.
Build and maintain rules.
3.
Remediate and mitigate risk.
4.
Detect authorization risk.
5.
Test and report the risk.
6.
Prevent the risk.
Questions 5
For which of the following tasks is a user administrator responsible? Note: There are 3 correct answers to this question.
A. Maintain user master records.
B. Assign users to profiles.
C. Activate profiles.
D. Maintain roles.
E. Assign users to roles.
Questions 6
You want to add a Customizing object to a role.
Which options are available in the Profile Generator (see attached screenshot)?
Note: There are 2 correct answers to this question.
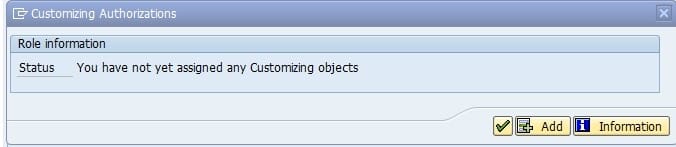
A. Enterprise IMG
B. IMG project view
C. SAP Reference IMG
D. IMG project
Questions 7
You have made changes to tables USOBX_C and USOBT_C. You want to transport these tables from the development environment to the testing environment.
Which transaction do you use to create this transport?
A. Maintain table (SM30)
B. User maintenance (SU01)
C. Profile generator: upgrade and first installation (SU25)
D. User information system (SUIM)
Questions 8
When you logon to the system with the SAP_AUDITOR_SA role, which of the following reports can be found in the Top 10 Security Reports folder of the Audit Information System (AIS)?
Note: There are 2 correct answers to this question.
A. Date Monitoring (S_PH0_48000450)
B. Analysis of Security Audit Log (SM20N)
C. IDoc List (RSEIDOC2)
D. Check Passwords of Standard Users (RSUSR003)
Questions 9
To work with the Audit Information System (AIS), which of the following steps do you have to execute? Note: There are 2 correct answers to this question.
A. Modify the user group.
B. Set up user master records.
C. Set up security audit log.
D. Modify the AIS role.
Questions 10
You are configuring an SAP NetWeaver AS ABAP system to allow authentication with x.509 client certificates issued by SAP NetWeaver single sign-on (SSO). When you test the connection with the standard SAP GUI, the system unexpectedly asks you for a password.
How can you avoid the additional logon in the standard SAP GUI?
A. Create a new SAP logon entry using the SNC name.
B. Set the parameter icm/server_port_2 with string VCLIENT = 2.
C. Map the client certificate of the user ID to the SAP NetWeaver AS ABAP user master record.
D. Import the User CA root certificate from the Secure Login Server.
Questions 11
Which of the following authorization objects must you assign to a user in SAP Solution Manager and in the SAP managed system to make sure that a trusted Remote Function Call connection is established?
A. S_RFC
B. S_RFC_TT
C. S_RFC_SHLP
D. S_RFCACL
Questions 12
Which transaction can you use to create background jobs?
A. SU10
B. PFCG
C. SM36
D. SA38
Questions 13
You have to assign multiple roles to multiple users. Which transaction allows you to do this efficiently?
A. SU03
B. SU01
C. SU10
D. SU02
