CAS-003 Online Practice Questions and Answers
Questions 4
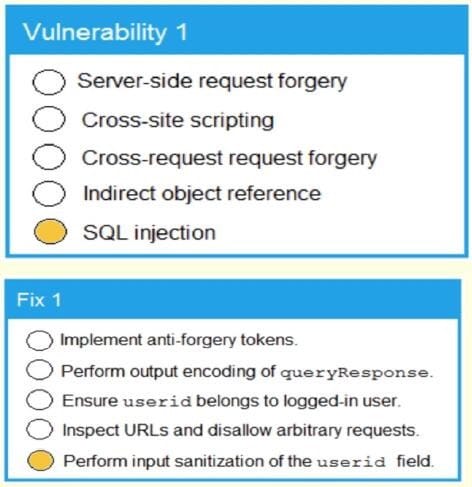
SIMULATION
A product development team has submitted code snippets for review pnor to release INSTRUCTIONS.
Analyze the code snippets and then select one vulnerability and one fix for each code snippet If at any time you would like to bang back the initial state of the simulation, please click the Reset All button.
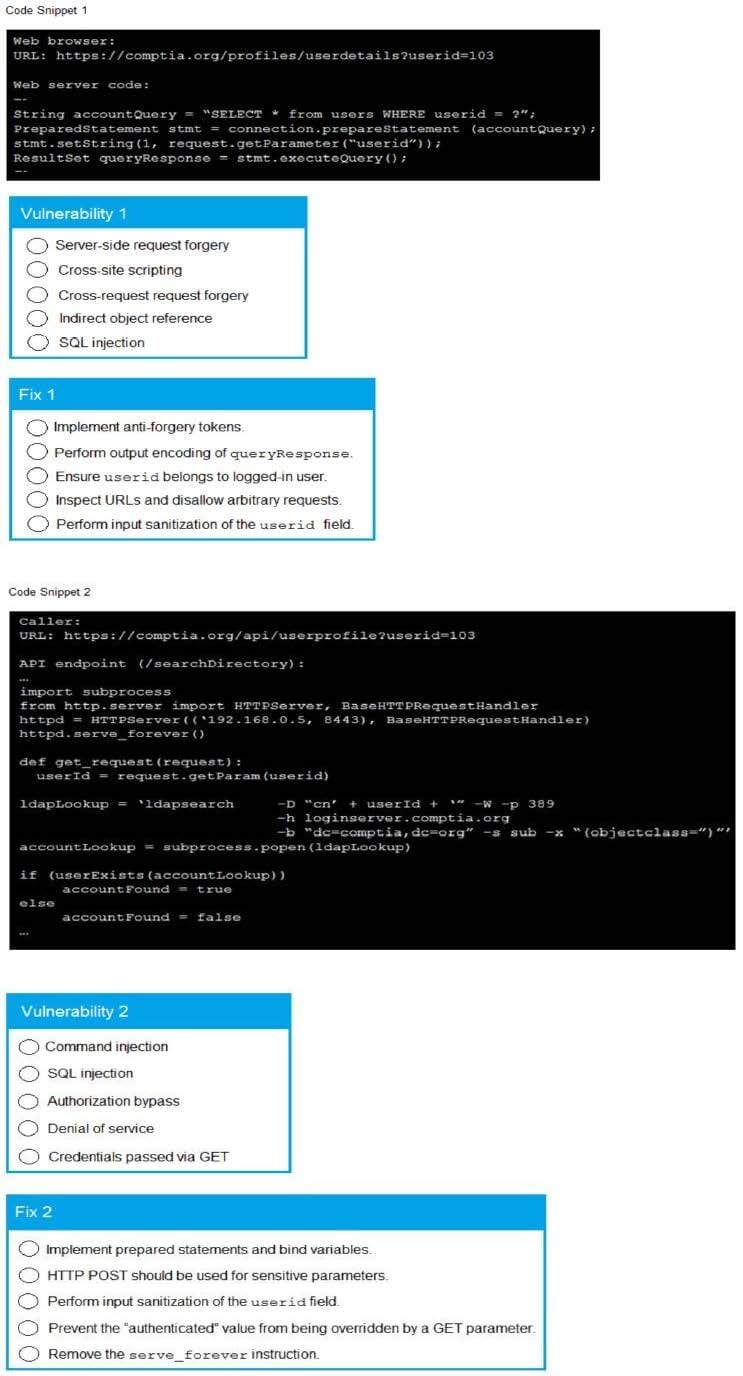
A. Check the answer in explanation below.
Questions 5
The security configuration management policy states that all patches must undergo testing procedures before being moved into production. The sec... analyst notices a single web application server has been downloading and applying patches during non-business hours without testing. There are no apparent adverse reaction, server functionality does not seem to be affected, and no malware was found after a scan. Which of the following action should the analyst take?
A. Reschedule the automated patching to occur during business hours.
B. Monitor the web application service for abnormal bandwidth consumption.
C. Create an incident ticket for anomalous activity.
D. Monitor the web application for service interruptions caused from the patching.
Questions 6
A multi-national company has a highly mobile workforce and minimal IT infrastructure. The company utilizes a BYOD and social media policy to integrate presence technology into global collaboration tools by individuals and teams. As a result of the dispersed employees and frequent international travel, the company is concerned about the safety of employees and their families when moving in and out of certain countries. Which of the following could the company view as a downside of using presence technology?
A. Insider threat
B. Network reconnaissance
C. Physical security
D. Industrial espionage
Questions 7
A security analyst is reviewing the corporate MDM settings and notices some disabled settings, which consequently permit users to download programs from untrusted developers and manually install them. After some conversations, it is confirmed that these settings were disabled to support the internal development of mobile applications. The security analyst is now recommending that developers and testers have a separate device profile allowing this, and that the rest of the organization's users do not have the ability to manually download and install untrusted applications. Which of the following settings should be toggled to achieve the goal? (Choose two.)
A. OTA updates
B. Remote wiping
C. Side loading
D. Sandboxing
E. Containerization
F. Signed applications
Questions 8
A security administrator is updating corporate policies to respond to an incident involving collusion between two systems administrators that went undetected for more than six months. Which of the following policies would have MOST likely uncovered the collusion sooner? (Choose two.)
A. Mandatory vacation
B. Separation of duties
C. Continuous monitoring
D. Incident response
E. Time-of-day restrictions
F. Job rotation
Questions 9
A newly hired Chief Information Security Officer (CISO) wants to understand how the organization's CIRT handles issues brought to their attention, but needs to be very cautious about impacting any systems. The MOST appropriate method to use would be:
A. an internal vulnerability assessment.
B. a red-team threat-hunt exercise.
C. a white-box penetration test.
D. a guided tabletop exercise.
Questions 10
A company suspects a web server may have been infiltrated by a rival corporation. The security engineer reviews the web server logs and finds the following:

ls -l -a /usr/beinz/public; cat ./config/db.yml
The security engineer looks at the code with a developer, and they determine the log entry is created when the following line is run:
system {"ls -l -a #(patch)"}
Which of the following is an appropriate security control the company should implement?
A. Restrict directory permission to read-only access.
B. Use server-side processing to avoid XSS vulnerabilities in path input.
C. Separate the items in the system call to prevent command injection.
D. Parameterize a query in the path variable to prevent SQL injection.
Questions 11
A security researcher at an organization is reviewing potential threats to the VoIP phone system infrastructure, which uses a gigabit Internet connection. The researcher finds a vulnerability and knows placing an IPS in front of the phone
system will mitigate the risk. The researcher gathers the following information about various IPS systems:
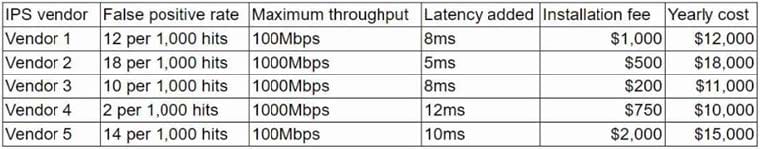
The organization is concerned about cost, but call quality is critical to its operations. Which of the following vendors would be BEST for the organization to choose?
A. Vendor 1
B. Vendor 2
C. Vendor 3
D. Vendor 4
E. Vendor 5
Questions 12
A security engineer at a company is designing a system to mitigate recent setbacks caused competitors that are beating the company to market with the new products. Several of the products incorporate propriety enhancements developed by the engineer's company. The network already includes a SEIM and a NIPS and requires 2FA for all user access. Which of the following system should the engineer consider NEXT to mitigate the associated risks?
A. DLP
B. Mail gateway
C. Data flow enforcement
D. UTM
Questions 13
A company recently experienced a period of rapid growth, and it now needs to move to a more scalable cloud-based solution. Historically, salespeople have maintained separate systems for information on competing customers to prevent the inadvertent disclosure of one customer's information to another customer.
Which of the following would be the BEST method to provide secure data separation?
A. Use a CRM tool to separate data stores
B. Migrate to a single-tenancy cloud infrastructure.
C. Employ network segmentation to provide isolation among salespeople
D. Implement an open-source public cloud CRM