CV0-003 Online Practice Questions and Answers
Questions 4
CORRECT TEXT
The QA team is testing a newly implemented clinical trial management (CTM) SaaS application that uses a business intelligence application for reporting. The UAT users were instructed to use HTTP and HTTPS.
Refer to the application dataflow:
1A -The end user accesses the application through a web browser to enter and view clinical data.
2A -The CTM application server reads/writes data to/from the database server.
1B -The end user accesses the application through a web browser to run reports on clinical data.
2B -The CTM application server makes a SOAP call on a non-privileged port to the BI application server.
3B -The BI application server gets the data from the database server and presents it to the CTM application server.
When UAT users try to access the application using https://ctm.app.com or http://ctm.app.com, they get a message stating: "Browser cannot display the webpage." The QA team has raised a ticket to troubleshoot the issue.
INSTRUCTIONS
You are a cloud engineer who is tasked with reviewing the firewall rules as well as virtual network settings.
You should ensure the firewall rules are allowing only the traffic based on the dataflow.
You have already verified the external DNS resolution and NAT are working.
Verify and appropriately configure the VLAN assignments and ACLs. Drag and drop the appropriate VLANs to each tier from the VLAN Tags table. Click on each Firewall to change ACLs as needed.
If at any time you would like to bring back the initial state of the simulation, please click the Reset All button.
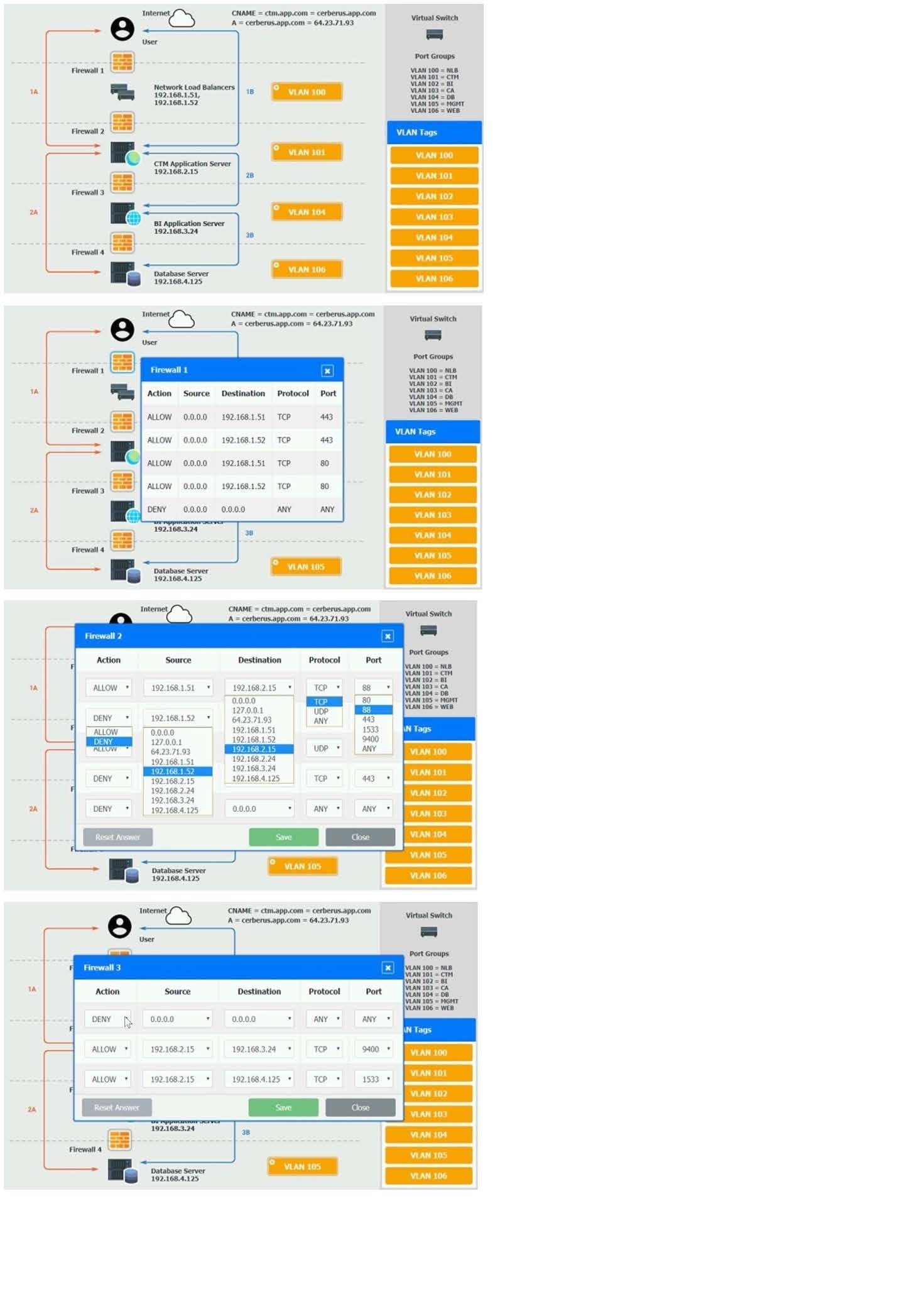
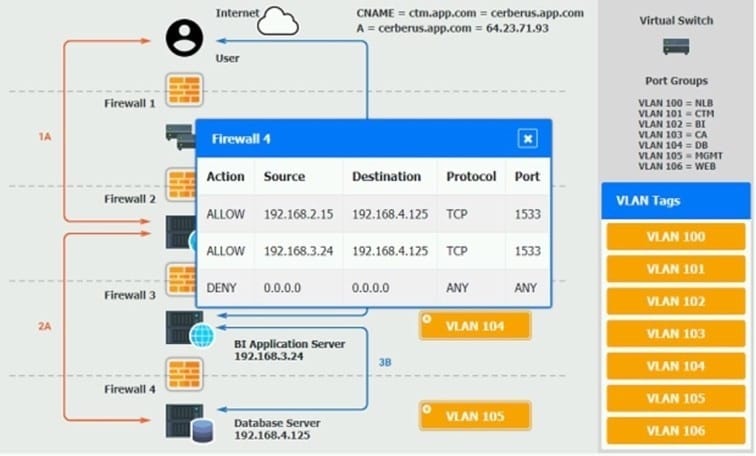
A. Check the answer in explanation.
Questions 5
A company is planning to migrate applications to a public cloud, and the Chief Information Officer (CIO) would like to know the cost per business unit for the applications in the cloud. Before the migration, which of the following should the administrator implement FIRST to assist with reporting the cost for each business unit?
A. An SLA report
B. Tagging
C. Quotas
D. Showback
Questions 6
Which of the following will mitigate the risk of users who have access to an instance modifying the system configurations?
A. Implement whole-disk encryption
B. Deploy the latest OS patches
C. Deploy an anti-malware solution
D. Implement mandatory access control
Questions 7
A company has decided to get multiple compliance and security certifications for its public cloud environment. However, the company has few staff members to handle the extra workload, and it has limited knowledge of the current infrastructure.
Which of the following will help the company meet the compliance requirements as quickly as possible?
A. DLP
B. CASB
C. FIM
D. NAC
Questions 8
A systems administrator is responding to an outage in a cloud environment that was caused by a network-based flooding attack. Which of the following should the administrator configure to mitigate the attack?
A. NIPS
B. Network overlay using GENEVE
C. DDoS protection
D. DoH
Questions 9
A support engineer wants to prevent users from running malware on several IaaS compute instances. Which of the following will BEST achieve this objective?
A. Encrypt all applications that users should not access.
B. Set the execute filesystem permissions on the desired applications only.
C. Implement an application whitelisting policy.
D. Disable file sharing on the instance.
Questions 10
A cloud administrator set up a link between the private and public cloud through a VPN tunnel. As part of the migration, a large set of files will be copied. Which of the following network ports are required from a security perspective?
A. 22, 53, 445
B. 22, 443, 445
C. 25, 123, 443
D. 137, 139, 445
Questions 11
A company is preparing a hypervisor environment to implement a database cluster. One of the requirements is to share the disks between the nodes of the cluster to access the same LUN. Which of the following protocols should the company use? (Choose two.)
A. CIFS
B. FTP
C. iSCSI
D. RAID 10
E. NFS
F. FC
Questions 12
A DevOps administrator is designing a new machine-learning platform. The application needs to be portable between public and private clouds and should be kept as small as possible. Which of the following approaches would BEST meet these requirements?
A. Virtual machines
B. Software as a service
C. Serverless computing
D. Containers
Questions 13
A web application has been configured to use auto-scaling for provisioning and deprovisioning more VMs according to the workload. The systems administrator deployed a new CI/CD tool to automate new releases of the web application. During the night, a script was deployed and configured to be executed by the VMs during bootstrapping. Now, the auto-scaling configuration is creating a new VM every five minutes. Which of the following actions will MOST likely resolve the issue?
A. Reducing the maximum threshold in the auto-scaling configuration
B. Debugging the script and redeploying it
C. Changing the automation tool because it is incompatible
D. Modifying the script to shut down the VM after five minutes
