GIAC Certified Penetration Tester: GPEN
Want to pass your GIAC Certified Penetration Tester GPEN exam in the very first attempt? Try Pass2lead! It is equally effective for both starters and IT professionals.
- Vendor: GIAC
- Exam Code: GPEN
- Exam Name: GIAC Certified Penetration Tester
- Certifications: GIAC Information Security
- Total Questions: 385 Q&As
- Updated on: Apr 09, 2024
- Note: Product instant download. Please sign in and click My account to download your product.

- Q&As Identical to the VCE Product
- Windows, Mac, Linux, Mobile Phone
- Printable PDF without Watermark
- Instant Download Access
- Download Free PDF Demo
- Includes 365 Days of Free Updates
VCE
- Q&As Identical to the PDF Product
- Windows Only
- Simulates a Real Exam Environment
- Review Test History and Performance
- Instant Download Access
- Includes 365 Days of Free Updates
Passing Certification Exams Made Easy
Everything you need prepare and quickly pass the tough certification exams the first time
- 99.5% pass rate
- 7 Years experience
- 7000+ IT Exam Q&As
- 70000+ satisfied customers
- 365 days Free Update
- 3 days of preparation before your test
- 100% Safe shopping experience
- 24/7 Support
GIAC GPEN Last Month Results
Free GPEN Exam Questions in PDF Format
Related GIAC Information Security Exams
GPEN Online Practice Questions and Answers
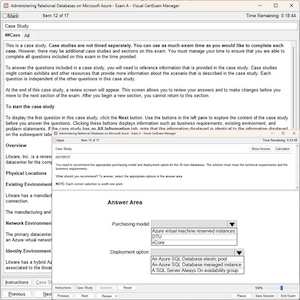
Questions 1
What is the purpose of the following command?
C:\>wmic /node:[target IP] /user:[admin-user] /password:[password] process call create [command]
A. Running a command on a remote Windows machine
B. Creating a service on a remote Windows machine
C. Creating an admin account on a remote Windows machine
D. Listing the running processes on a remote windows machine
Questions 2
How does OWASP ZAP function when used for performing web application assessments?
A. It is a non-transparent proxy that sits between your web browser and the targetapplication.
B. It is a transparent policy proxy that sits between Java servers and |SP web pages.
C. It is a non-transparent proxy that passively sniffs network traffic for HTTPvulnerabilities.
D. It is a transparent proxy that sits between a target application and the backenddatabase.
Questions 3
Adam, a malicious hacker, hides a hacking tool from a system administrator of his company by using Alternate Data Streams (ADS) feature. Which of the following statements is true in context with the above scenario?
A. Adam is using NTFS file system.
B. Alternate Data Streams is a feature of Linux operating system.
C. Adam is using FAT file system.
D. Adam's system runs on Microsoft Windows 98 operating system.
Reviews
-
This dumps is valid, and this dumps is the only study material i used for this exam. Surprisingly i met the same question in the exam, so i passed the exam without doubt. Thanks for this dumps and i will recommend it to my friends.
-
Dumps are valid. I passed my exam this morning. Few questions are different with the Qs from the dumps but never mind. I passed. Thank you. Good luck to you all.
-
Thanks for your help. I passed my exam yesterday with the full points! Great job.
-
In the morning i received the good news that I have passed the exam with good marks. I'm so happy for that. Thanks for the help of this material.
-
Very useful study material, thanks the help of this dumps .
-
Valid study material.Recommend strongly.
-
I have cleared that i passed the exam today. Thanks so much.
-
Answers are correct. Questions are valid.Recommend strongly.
-
took the exams yesterday and passed. I was very scared at first because the labs came in first so I was spending like 10 to 13mins so I started rushing after the first three labs thinking that I will have more labs. I ended up finishing the exam in an hour..d dumps are valid. I tink there is a new lab. good success
-
This dumps is very very valid. I passed this week with a satisfied score. ALL questions were from this file.

 Printable PDF
Printable PDF