JN0-348 Online Practice Questions and Answers
Questions 4
You have a conference room with an open network port that is used by employees to connect to the network. You are concerned about rogue switches being connected to this port.
Which two features should you enable on your switch to limit access to this port? (Choose two.)
A. DHCP snooping
B. dynamic ARP inspection
C. MAC limiting
D. 802.1X
Questions 5
Which two port security features use the DHCP snooping database for additional port security? (Choose two.)
A. dynamic ARP inspection
B. MACsec
C. IP Source Guard
D. MAC learning
Questions 6
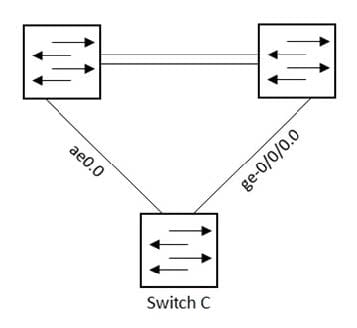
Referring to the exhibit, which configuration will force traffic to always use ae0.0 as long as it is active?
A. B. C. D.
Questions 7
You configured a GRE tunnel that traverses a path using default MTU settings. You want to ensure that packets are not dropped of fragmented.
In this scenario, what is the maximum packet size that would traverse the GRE tunnel?
A. 1500
B. 1400
C. 1524
D. 1476
Questions 8
Which three mechanisms are associated with the bridging process? (Choose three.)
A. blocking
B. flooding
C. aging
D. filtering
E. listening
Questions 9
Which two situations would cause dynamic ARP inspection to drop traffic? (Choose two.)
A. if no IP-to-MAC address entry exists in the DHCP snooping database
B. if the IP address in the ARP packet is deemed invalid
C. if the requested MAC address exceeds the configured limit on the port
D. if the ARP packet comes from a port that has been configured as trusted
Questions 10
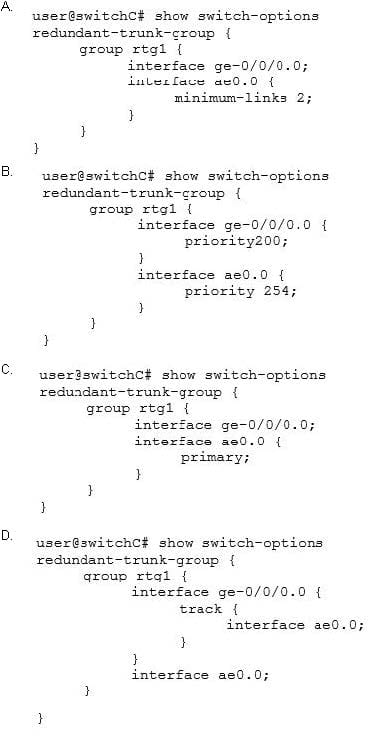
Click the Exhibit button.
Referring to the exhibit, which router becomes the OSPF DR when all routers are powered on at the same time?
A. R3
B. R4
C. R1
D. R2
Questions 11
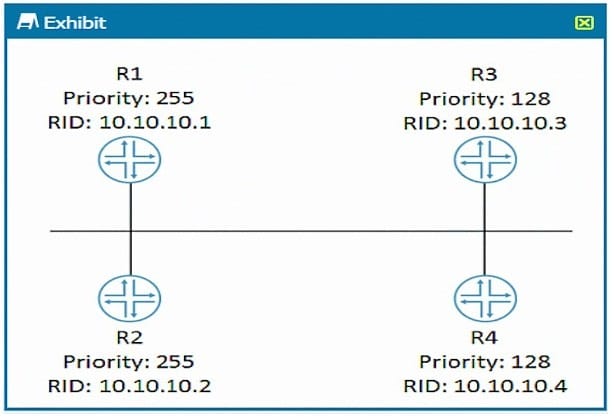
Click the Exhibit button.
Referring to the exhibit, what is the problem?
A. The LAG member interfaces are configured across different line cards
B. LAG requires more than two member links
C. LACP is required for LAG to work
D. Aggregated interfaces must be defined under the chassis stanza
Questions 12
Click the Exhibit button.
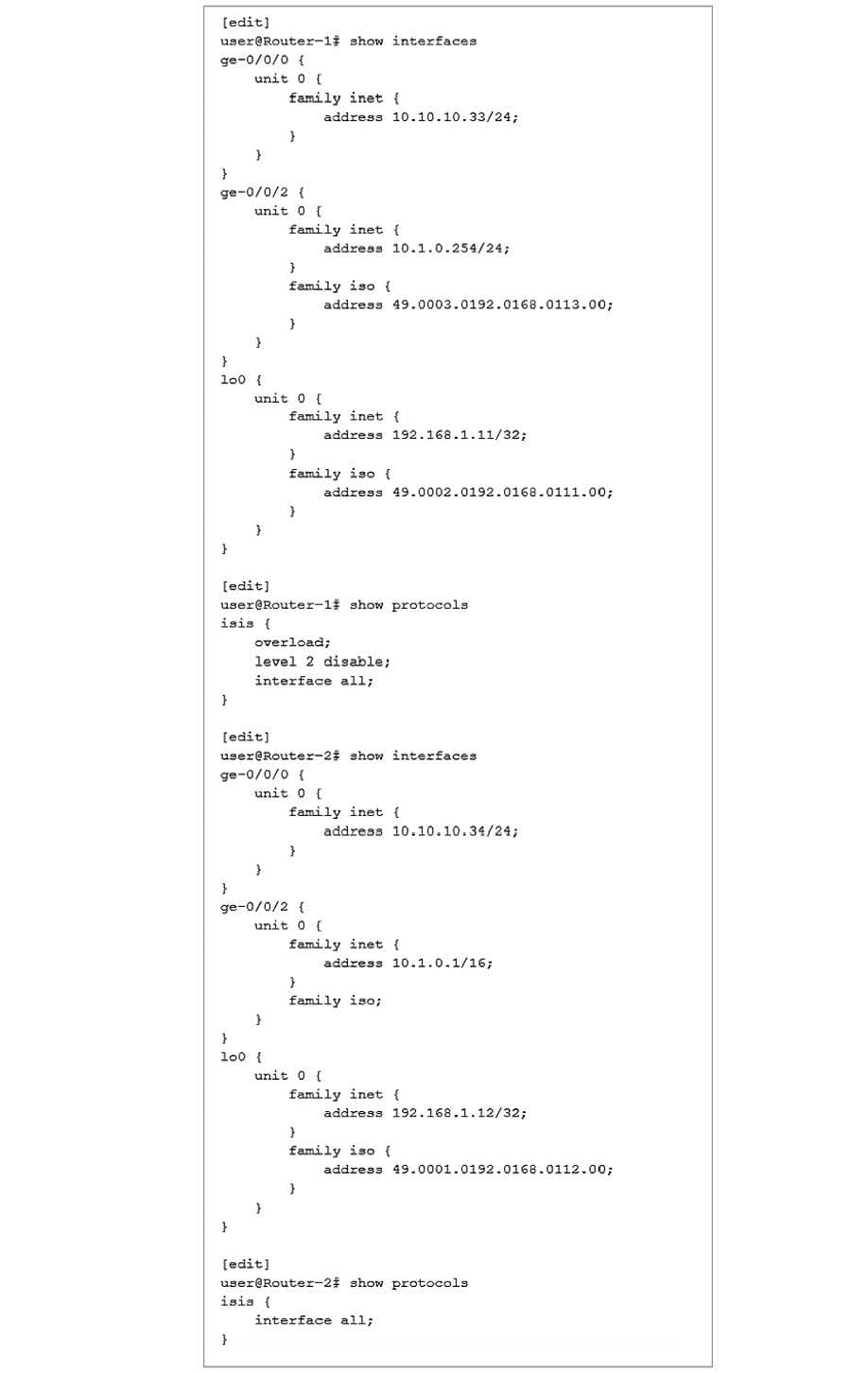
Referring to the exhibit, Router-1 and Router-2 are failing to form an IS-IS adjacency.
What should you do to solve the problem?
A. Remove the overloaded statement from Router-1.
B. Change the IP subnet masks to match on the ge-0/0/2 interfaces of both routers.
C. Change the ISO areas on the lo0 interfaces to match on both routers.
D. Remove the ISO address from ge-0/0/2 on Router-1.
Questions 13
You want to use filter-based forwarding (FBF) to forward traffic sourced from subnet 10.0.0.0/24 to a specific destination.
Which two routing instance types would enable you to accomplish this task? (Choose two.)
A. virtual switch
B. virtual routing and forwarding
C. virtual router
D. forwarding
