MS-500 Online Practice Questions and Answers
Questions 4
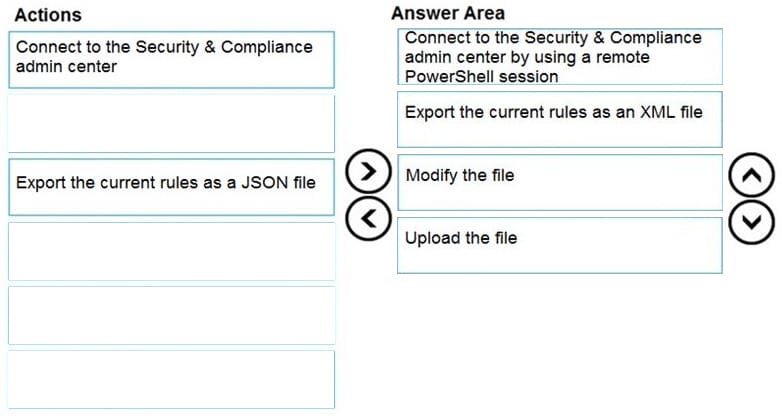
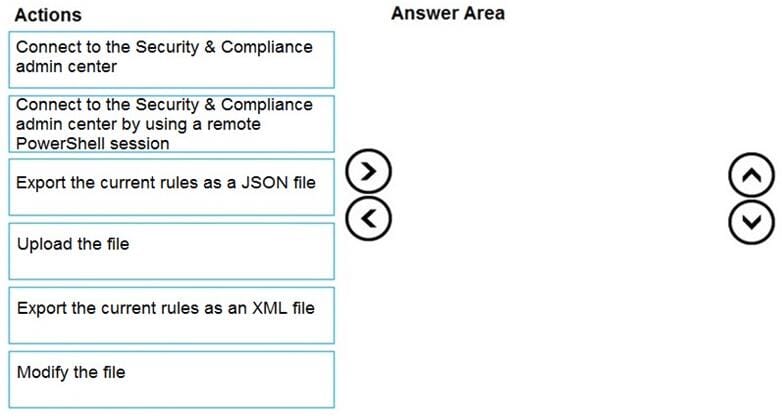
DRAG DROP
You have a Microsoft 365 subscription.
You need to include a custom sensitive information type in Data Subject Request (DSR) cases.
Which four actions should you perform in sequence? To answer, move the appropriate actions from the list of actions to the answer area and arrange them in the correct order.
Select and Place:
Questions 5
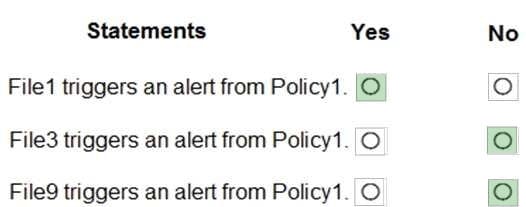
HOTSPOT
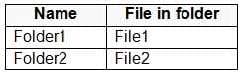
You have a Microsoft 365 subscription that contains a Microsoft SharePoint Online site named Site1. Site1 contains the folders shown in the following table.
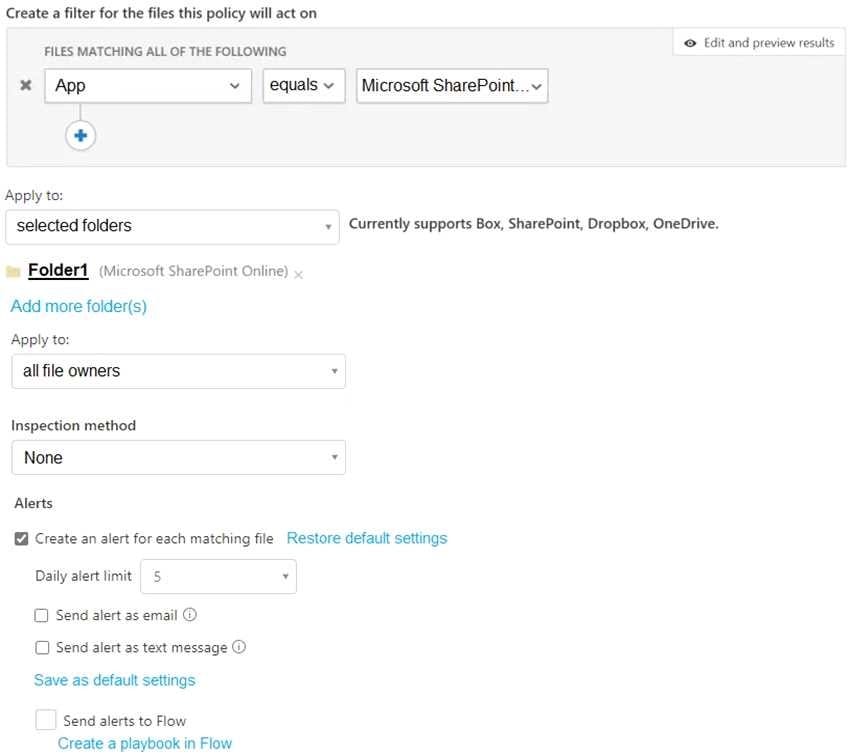
At 09:00, you create a Microsoft Cloud App Security policy named Policy1 as shown in the following exhibit.
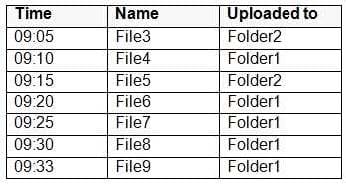
After you create Policy1, you upload files to Site1 as shown in the following table.
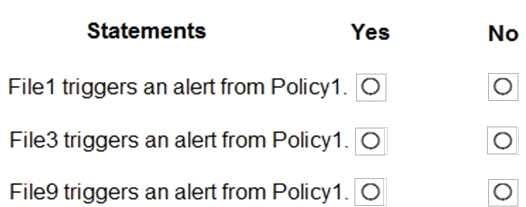
For each of the following statements, select Yes if the statement is true. Otherwise, select No. NOTE: Each correct selection is worth one point.
Hot Area:
Questions 6
You need to ensure that a user named Allan Deyoung receives incident reports when email messages that contain data covered by the U.K. Data Protection Act are sent outside of your organization.
To complete this task, sign in to the Microsoft 365 admin center.
Questions 7
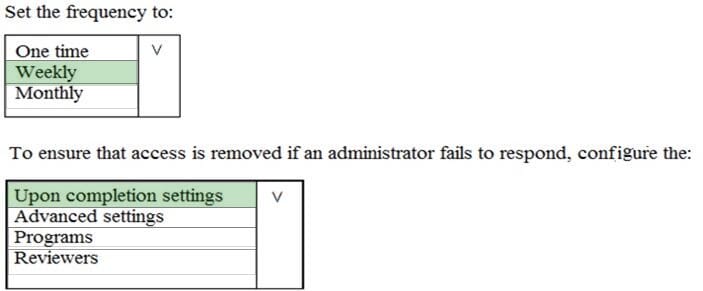
HOTSPOT
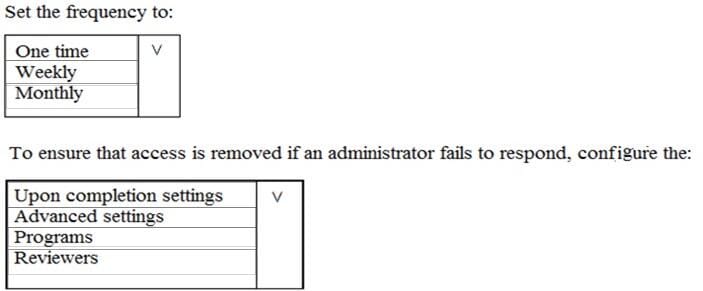
You plan to configure an access review to meet the security requirements for the workload administrators. You create an access review policy and specify the scope and a group.
Which other settings should you configure? To answer, select the appropriate options in the answer area.
NOTE: Each correct selection is worth one point.
Hot Area:
Questions 8
You have a Microsoft 365 subscription that includes a user named User1.
You have a conditional access policy that applies to Microsoft Exchange Online. The conditional access policy is configured to use Conditional Access App Control.
You need to create a Microsoft Cloud App Security policy that blocks User1 from printing from Exchange Online.
Which type of Cloud App Security policy should you create?
A. an app permission policy
B. an activity policy
C. a Cloud Discovery anomaly detection policy
D. a session policy
Questions 9
You have a Microsoft 365 tenant.
You need to implement a policy to enforce the following requirements:
If a user uses a Windows 10 device that is NOT hybrid Azure Active Directory (Azure AD) joined, the user must be allowed to connect to Microsoft SharePoint Online only from a web browser. I he user must be prevented from downloading
files or syncing files from SharePoint Online.
If a user uses a Windows 10 device that is hybrid Azure AD joined, the user must be able connect to SharePoint Online from any client application, download files, and sync files.
What should you create?
A. a conditional access policy in Azure AD that has Client apps conditions configured
B. a compliance policy in Microsoft Endpoint Manager that has the Device Health settings configured
C. a compliance policy in Microsoft Endpoint Manager that has the Device Properties settings configured
D. a conditional access policy in Azure AD that has Session controls configured
Questions 10
Your network contains an on-premises Active Directory domain. The domain contains servers that run Windows Server and have advanced auditing enabled. The security logs of the servers are collected by using a third-party SIEM solution.
You purchase a Microsoft 365 subscription and plan to deploy Azure Advanced Threat Protection (ATP) by using standalone sensors. You need to ensure that you can detect when sensitive groups are modified and when malicious services
are created.
What should you do?
A. Configure Azure ATP notifications
B. Configure Event Forwarding on the domain controllers
C. Configure auditing in the Office 365 Security and Compliance center
D. Modify the Domain synchronizer candidate settings on the Azure ATP sensors
Questions 11
You have a Microsoft 365 E5 subscription that contains the users shown in the following table.
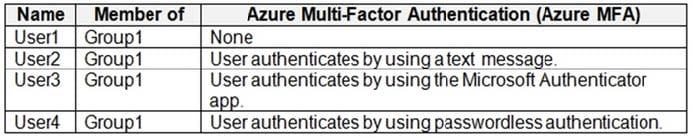
You enable the authentication methods registration campaign and configure the Microsoft Authenticator method for Group1.
Which users will be prompted to configure authentication during sign in?
A. User1 only
B. User2 only
C. User2 and User3 only
D. User1 and User2 only
E. User2 and User3 only
F. User1, User2, and User3 only
Questions 12
You have an Azure Sentinel workspace that has an Azure Active Directory (Azure AD) connector and a Microsoft Office 365 connector.
You need to use a Fusion rule template to detect multistage attacks in which users sign in by using compromised credentials, and then delete multiple files from Microsoft OneDrive.
Based on the Fusion rule template, you create an active rule that has the default settings.
What should you do next?
A. Add data connectors.
B. Add a workbook.
C. Add a playbook.
D. Create a custom rule template.
Questions 13
Note: This question is part of a series of questions that present the same scenario. Each question in the series contains a unique solution that might meet the stated goals. Some question sets might have more than one correct solution, while
others might not have a correct solution.
After you answer a question in this section, you will NOT be able to return to it. As a result, these questions will not appear in the review screen.
Your on-premises network contains a server that runs Windows Server 2019, computers that run Windows 10, macOS, or Linux, and a firewall that utilizes syslog.
You have a Microsoft 365 E5 subscription that uses Microsoft Defender for Endpoint. All the computers are onboarded to Microsoft Defender for Endpoint.
You are implementing Microsoft Defender for Cloud Apps.
You need to discover which cloud apps are accessed from the computers.
Solution: You install an Azure Arc agent on the workstations.
Does this meet the goal?
A. Yes
B. No