NSE4_FGT-6.2 Online Practice Questions and Answers
Questions 4
Which statements about a One-to-One IP pool are true? (Choose two.)
A. It is used for destination NAT.
B. It allows the fixed mapping of an internal address range to an external address range.
C. It does not use port address translation.
D. It allows the configuration of ARP replies.
Questions 5
An administrator has configured central DNAT and virtual IPs. Which of the following can be selected in the firewall policy Destination field?
A. A VIP group
B. The mapped IP address object of the VIP object
C. A VIP object
D. An IP pool
Questions 6
Which of the following conditions must be met in order for a web browser to trust a web server certificate signed by a third-party CA?
A. The public key of the web server certificate must be installed on the browser.
B. The web-server certificate must be installed on the browser.
C. The CA certificate that signed the web-server certificate must be installed on the browser.
D. The private key of the CA certificate that signed the browser certificate must be installed on the browser.
Questions 7
Which statements correctly describe transparent mode operation? (Choose three.)
A. All interfaces of the transparent mode FortiGate device must be on different IP subnets.
B. Ethernet packets are forwarded based on destination MAC addresses, not IP addresses.
C. The transparent FortiGate is visible to network hosts in an IP traceroute.
D. It permits inline traffic inspection and firewalling without changing the IP scheme of the network.
E. FortiGate acts as transparent bridge and forwards traffic at Layer 2.
Questions 8
What settings must you configure to ensure FortiGate generates logs for web filter activity on a firewall policy called Full Access? (Choose two.)
A. Enable Event Logging.
B. Enable a web filter security profile on the Full Access firewall policy.
C. Enable Log Allowed Traffic on the Full Access firewall policy.
D. Enable disk logging.
Questions 9
When browsing to an internal web server using a web-mode SSL VPN bookmark, which IP address is used as the source of the HTTP request?
A. remote user's public IP address
B. The public IP address of the FortiGate device.
C. The remote user's virtual IP address.
D. The internal IP address of the FortiGate device.
Questions 10
In a high availability (HA) cluster operating in active-active mode, which of the following correctly describes the path taken by the SYN packet of an HTTP session that is offloaded to a secondary FortiGate?
A. Client > primary FortiGate> secondary FortiGate> primary FortiGate> web server.
B. Client > secondary FortiGate> web server.
C. Clinet >secondary FortiGate> primary FortiGate> web server.
D. Client> primary FortiGate> secondary FortiGate> web server.
Questions 11
Which statements best describe auto discovery VPN (ADVPN). (Choose two.)
A. It recommends the use of dynamic routing protocols so that spokes can learn the routes to other spokes.
B. ADVPN is only supported with IKEv2.
C. IPSec tunnels are negotiated dynamically between spokes.
D. Every spoke requires a static tunnel to be configured to other spokes so that phase 1 and phase 2 proposals are defined in advance.
Questions 12
The FSSO Collector Agent set to advanced access mode for the Windows Active Directory uses which of the following?
A. LDAP convention B. NTLM convention
C. Windows convention ?NetBios\Username
D. RSSO convention
Questions 13
View the exhibit.
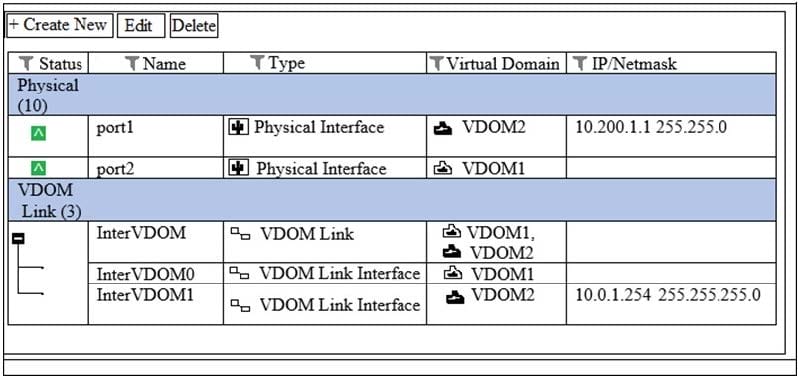
VDOM1 is operating in transparent mode VDOM2 is operating in NAT Route mode. There is an inteface VDOM link between both VDOMs. A client workstation with the IP address 10.0.1.10/24 is connected to port2. A web server with the IP address 10.200.1.2/24 is connected to port1. What is required in the FortiGate configuration to route and allow connections from the client workstation to the web server? (Choose two.)
A. A static or dynamic route in VDOM2 with the subnet 10.0.1.0/24 as the destination.
B. A static or dynamic route in VDOM1 with the subnet 10.200.1.0/24 as the destination.
C. One firewall policy in VDOM1 with port2 as the source interface and InterVDOM0 as the destination interface.
D. One firewall policy in VDOM2 with InterVDOM1 as the source interface and port1 as the destination interface.
