NSE6_FWF-6.4 Online Practice Questions and Answers
Questions 4
When configuring Auto TX Power control on an AP radio, which two statements best describe how the radio responds? (Choose two.)
A. When the AP detects any other wireless signal stronger that -70 dBm, it will reduce its transmission power until it reaches the minimum configured TX power limit.
B. When the AP detects PF Interference from an unknown source such as a cordless phone with a signal stronger that -70 dBm, it will increase its transmission power until it reaches the maximum configured TX power limit.
C. When the AP detects any wireless client signal weaker than -70 dBm, it will reduce its transmission power until it reaches the maximum configured TX power limit.
D. When the AP detects any interference from a trusted neighboring AP stronger that -70 dBm, it will reduce its transmission power until it reaches the minimum configured TX power limit.
Questions 5
Refer to the exhibits.
Exhibit A.
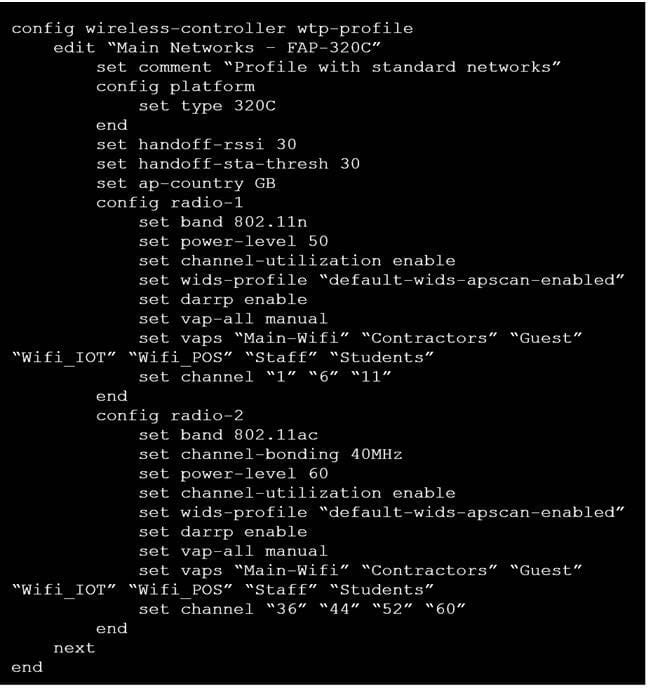
Exhibit B.
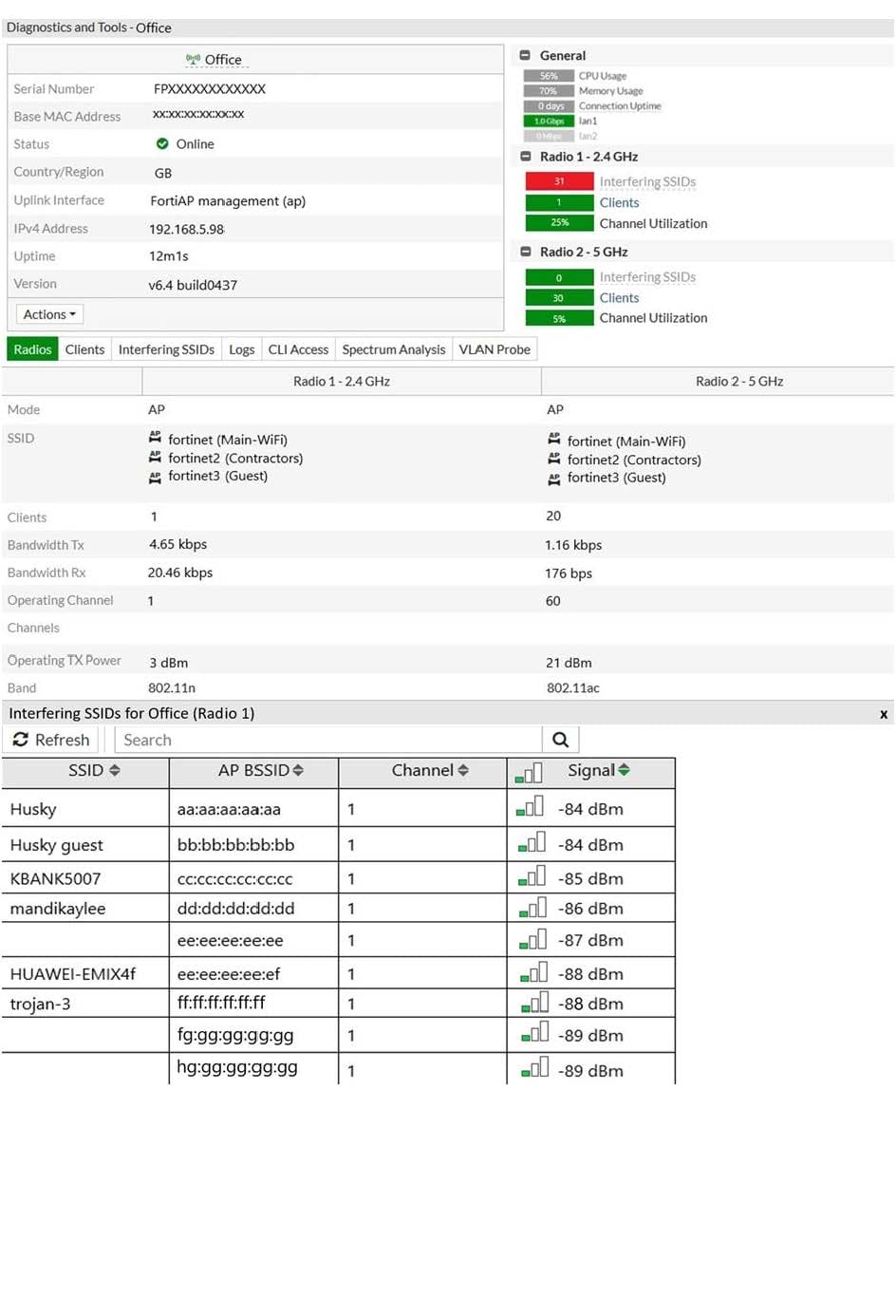
Exhibit C.
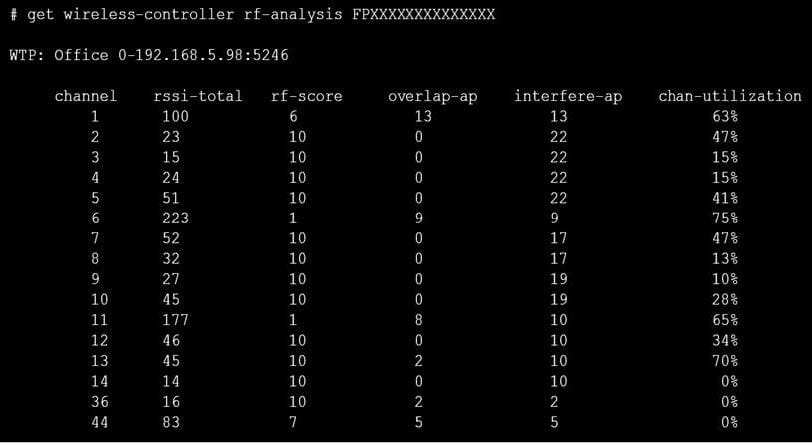
A wireless network has been installed in a small office building and is being used by a business to connect its wireless clients. The network is used for multiple purposes, including corporate access, guest access, and connecting point-of-sale and IoТ devices.
Users connecting to the guest network located in the reception area are reporting slow performance. The network administrator is reviewing the information shown in the exhibits as part of the ongoing investigation of the problem. They show the profile used for the AP and the controller RF analysis output together with a screenshot of the GUI showing a summary of the AP and its neighboring APs.
To improve performance for the users connecting to the guest network in this area, which configuration change is most likely to improve performance?
A. Increase the transmission power of the AP radios
B. Enable frequency handoff on the AP to band steer clients
C. Reduce the number of wireless networks being broadcast by the AP
D. Install another AP in the reception area to improve available bandwidth
Questions 6
When enabling security fabric on the FortiGate interface to manage FortiAPs, which two types of communication channels are established between FortiGate and FortiAPs? (Choose two.)
A. Control channels
B. Security channels
C. FortLink channels
D. Data channels
Questions 7
Which two configurations are compatible for Wireless Single Sign-On (WSSO)? (Choose two.)
A. A VAP configured for captive portal authentication
B. A VAP configured for WPA2 or 3 Enterprise
C. A VAP configured to authenticate locally on FortiGate
D. A VAP configured to authenticate using a radius server
Questions 8
Which administrative access method must be enabled on a FortiGate interface to allow APs to connect and function?
A. Security Fabric
B. SSH
C. HTTPS
D. FortiTelemetry
Questions 9
You are investigating a wireless performance issue and you are trying to audit the neighboring APs in the PF environment. You review the Rogue APs widget on the GUI but it is empty, despite the known presence of other APs.
Which configuration change will allow neighboring APs to be successfully detected?
A. Enable Locate WiFi clients when not connected in the relevant AP profiles.
B. Enable Monitor channel utilization on the relevant AP profiles.
C. Ensure that all allowed channels are enabled for the AP radios.
D. Enable Radio resource provisioning on the relevant AP profiles.
Questions 10
Which two roles does FortiPresence analytics assist in generating presence reports? (Choose two.)
A. Gathering details about on site visitors
B. Predicting the number of guest users visiting on-site
C. Comparing current data with historical records
D. Reporting potential threats by guests on site
Questions 11
Which statement describes FortiPresence location map functionality?
A. Provides real-time insight into user movements
B. Provides real-time insight into user online activity
C. Provides real-time insight into user purchase activity
D. Provides real-time insight into user usage stats
Questions 12
Which statement is correct about security profiles on FortiAP devices?
A. Security profiles on FortiAP devices can use FortiGate subscription to inspect the traffic
B. Only bridge mode SSIDs can apply the security profiles
C. Disable DTLS on FortiAP
D. FortiGate performs inspection the wireless traffic
Questions 13
How are wireless clients assigned to a dynamic VLAN configured for hash mode?
A. Using the current number of wireless clients connected to the SSID and the number of IPs available in the least busy VLAN
B. Using the current number of wireless clients connected to the SSID and the number of clients allocated to each of the VLANs
C. Using the current number of wireless clients connected to the SSID and the number of VLANs available in the pool
D. Using the current number of wireless clients connected to the SSID and the group the FortiAP is a member of
