PCNSA Online Practice Questions and Answers
Questions 4
How are Application Fillers or Application Groups used in firewall policy?
A. An Application Filter is a static way of grouping applications and can be configured as a nested member of an Application Group
B. An Application Filter is a dynamic way to group applications and can be configured as a nested member of an Application Group
C. An Application Group is a dynamic way of grouping applications and can be configured as a nested member of an Application Group
D. An Application Group is a static way of grouping applications and cannot be configured as a nested member of Application Group
Questions 5
An administrator wants to create a NAT policy to allow multiple source IP addresses to be translated to the same public IP address. What is the most appropriate NAT policy to achieve this?
A. Dynamic IP and Port
B. Dynamic IP
C. Static IP
D. Destination
Questions 6
Which object would an administrator create to enable access to all applications in the office-programs subcategory?
A. application filter
B. URL category
C. HIP profile
D. application group
Questions 7
The NetSec Manager asked to create a new firewall Local Administrator profile with customized privileges named New_Admin. This new administrator has to authenticate without inserting any username or password to access the WebUI. What steps should the administrator follow to create the New_Admin Administrator profile?
A. 1. Set the Authentication profile to Local.
2.
Select the "Use only client certificate authentication" check box.
3.
Set Role to Role Based.
B. 1. Select the "Use only client certificate authentication" check box.
2.
Set Role to Dynamic.
3.
Issue to the Client a Certificate with Certificate Name = New Admin
C. 1. Select the "Use only client certificate authentication" check box.
2.
Set Role to Dynamic.
3.
Issue to the Client a Certificate with Common Name = New_Admin
D.
1. Select the "Use only client certificate authentication" check box.
2. Set Role to Role Based.
3.
Issue to the Client a Certificate with Common Name = New Admin
Questions 8
Review the screenshot below. Which statement is correct about the information it contains?
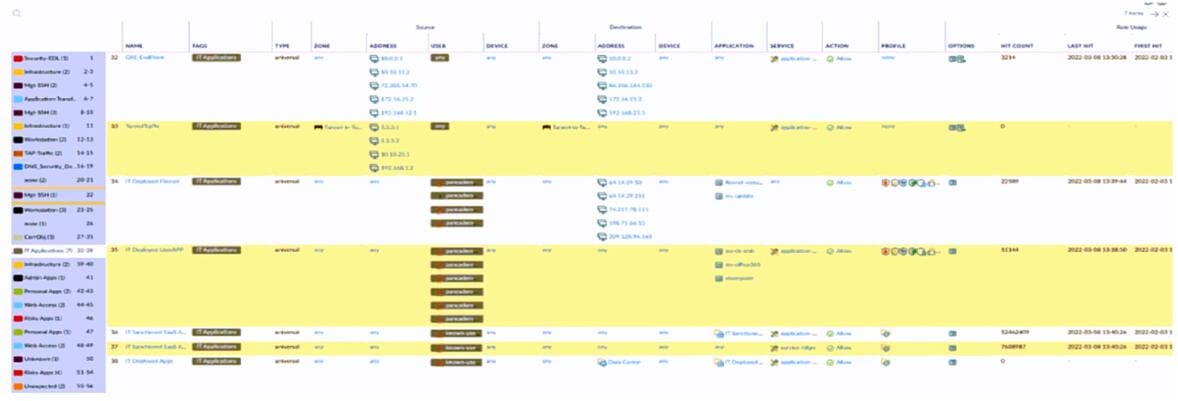
A. Highlight Unused Rules is checked.
B. Tunnel Traffic has the High Risk tag applied.
C. There are six Security policy rules on this firewall.
D. View Rulebase as Groups is checked.
Questions 9
Which update option is not available to administrators?
A. New Spyware Notifications
B. New URLs
C. New Application Signatures
D. New Malicious Domains
E. New Antivirus Signatures
Questions 10
Which User-ID mapping method should be used for an environment with clients that do not authenticate to Windows Active Directory?
A. Windows session monitoring via a domain controller
B. passive server monitoring using the Windows-based agent
C. Captive Portal
D. passive server monitoring using a PAN-OS integrated User-ID agent
Questions 11
Which three filter columns are available when setting up an Application Filter? (Choose three.)
A. Parent App
B. Category
C. Risk
D. Standard Ports
E. Subcategory
Questions 12
How does an administrator schedule an Applications and Threats dynamic update while delaying installation of the update for a certain amount of time?
A. Disable automatic updates during weekdays
B. Automatically "download and install" but with the "disable new applications" option used
C. Automatically "download only" and then install Applications and Threats later, after the administrator approves the update
D. Configure the option for "Threshold"
Questions 13
Which attribute can a dynamic address group use as a filtering condition to determine its membership?
A. tag
B. wildcard mask
C. IP address
D. subnet mask
