PT0-001 Online Practice Questions and Answers
Questions 4
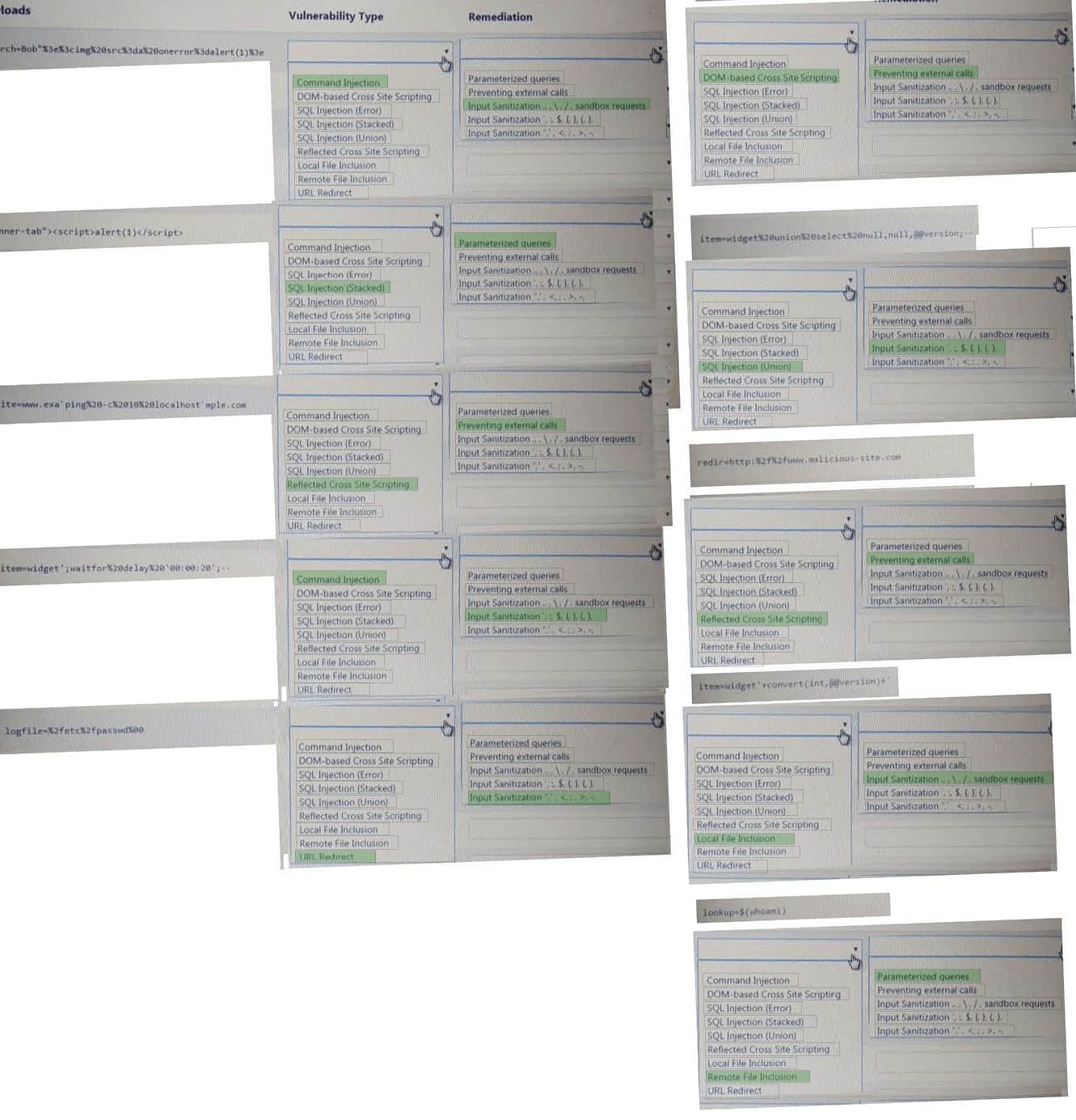
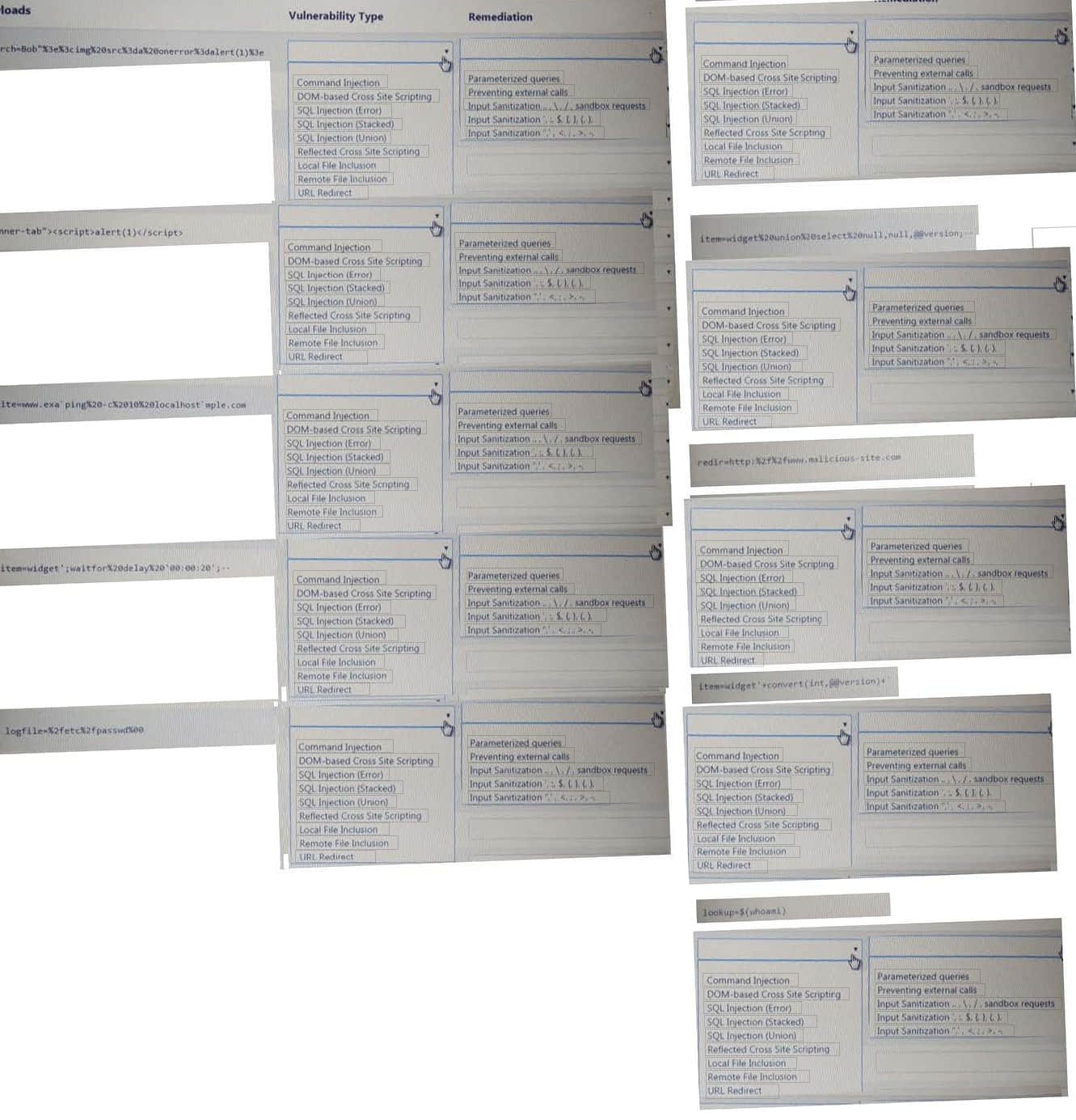
HOTSPOT
You are a security analyst tasked with hardening a web server.
You have been given a list of HTTP payloads that were flagged as malicious.
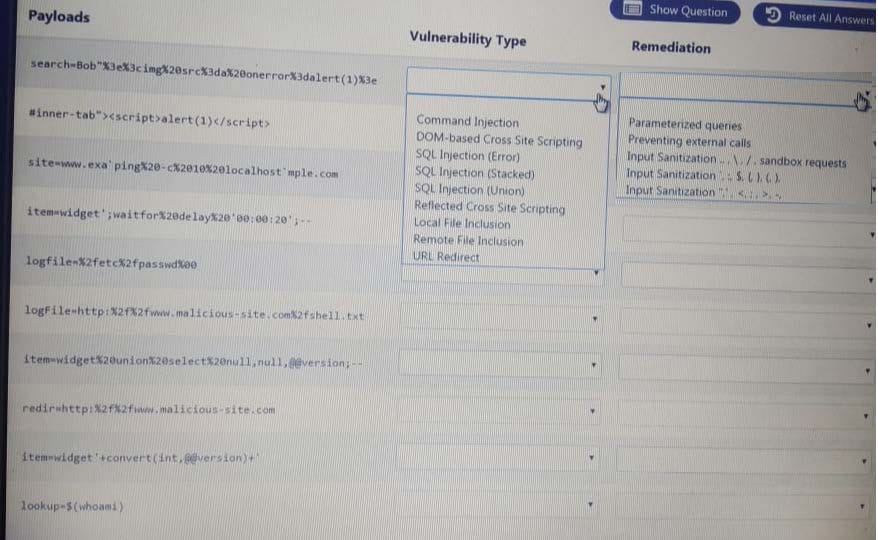
Hot Area:
Questions 5
If a security consultant comes across a password hash that resembles the following b117 525b3454 7Oc29ca3dBaeOb556ba8 Which of the following formats is the correct hash type?
A. Kerberos
B. NetNTLMvl
C. NTLM
D. SHA-1
Questions 6
A penetration testet is attempting to capture a handshake between a client and an access point by monitoring a WPA2-PSK secured wireless network The (ester is monitoring the correct channel tor the identified network but has been unsuccessful in capturing a handshake Given this scenario, which of the following attacks would BEST assist the tester in obtaining this handshake?
A. Karma attack
B. Deauthentication attack
C. Fragmentation attack
D. SSID broadcast flood
Questions 7
A client is asking a penetration tester to evaluate a new web application for availability. Which of the following types of attacks should the tester use?
A. TCP SYN flood
B. SQL injection
C. xss
D. XMAS scan
Questions 8
A penetration tester calls human resources and begins asking open-ended questions Which of the following social engineering techniques is the penetration tester using?
A. Interrogation
B. Elicitation
C. Impersonation
D. Spear phishing
Questions 9
A company received a report with the following finding While on the internal network the penetration tester was able to successfully capture SMB broadcasted user ID and password information on the network and decode this information This allowed the penetration tester to then join their own computer to the ABC domain
Which of the following remediation's are appropriate for the reported findings'? (Select TWO)
A. Set the Schedule Task Service from Automatic to Disabled
B. Enable network-level authentication
C. Remove the ability from Domain Users to join domain computers to the network
D. Set the netlogon service from Automatic to Disabled
E. Set up a SIEM alert to monitor Domain joined machines
F. Set "Digitally sign network communications" to Always
Questions 10
A consultant is attempting to harvest credentials from unsecure network protocols in use by the organization. Which of the following commands should the consultant use?
A. Tcmpump
B. John
C. Hashcat
D. nc
Questions 11
A penetration tester discovers an anonymous FTP server that is sharing the C:\drive. Which of the following is the BEST exploit?
A. Place a batch script in the startup folder for all users.
B. Change a service binary location path to point to the tester's own payload.
C. Escalate the tester's privileges to SYSTEM using the at.exe command.
D. Download, modify, and reupload a compromised registry to obtain code execution.
Questions 12
A systems security engineer is preparing to conduct a security assessment of some new applications. The applications were provided to the engineer as a set that contains only JAR files. Which of the following would be the MOST detailed method to gather information on the inner workings of these applications?
A. Launch the applications and use dynamic software analysis tools, including fuzz testing.
B. Use a static code analyzer on the JAR files to look for code quality deficiencies.
C. Decompile the applications to approximate source code and then conduct a manual review.
D. Review the details and extensions of the certificate used to digitally sign the code and the application.
Questions 13
A penetration tester is performing a black-box test of a client web application, and the scan host is unable to access it. The client has sent screenshots showing the system is functioning correctly. Which of the following is MOST likely the issue?
A. The penetration tester was not provided with a WSDL file.
B. The penetration tester needs an OAuth bearer token.
C. The tester has provided an incorrect password for the application.
D. An IPS/WAF whitelist is in place to protect the environment.