SC-200 Online Practice Questions and Answers
Questions 4
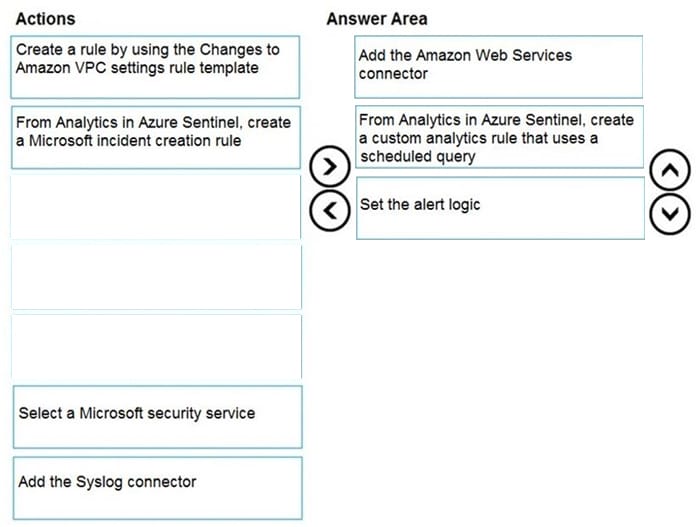
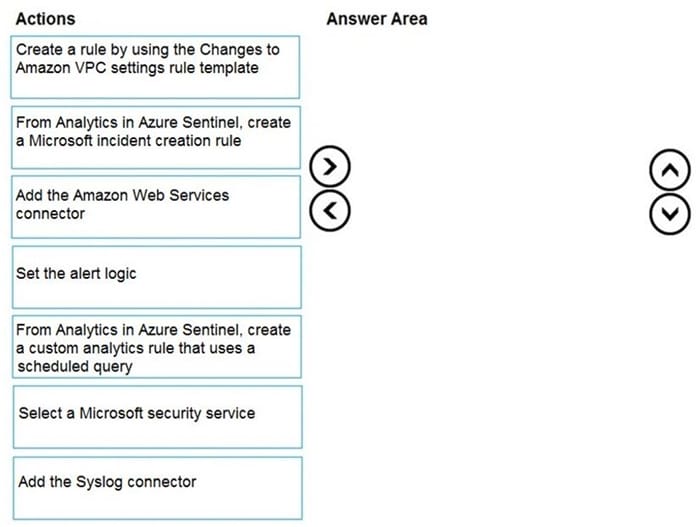
DRAG DROP
You need to use an Azure Sentinel analytics rule to search for specific criteria in Amazon Web Services (AWS) logs and to generate incidents.
Which three actions should you perform in sequence? To answer, move the appropriate actions from the list of actions to the answer area and arrange them in the correct order.
Select and Place:
Questions 5
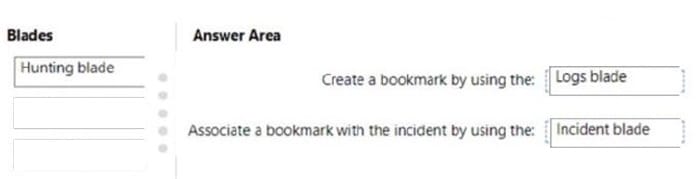
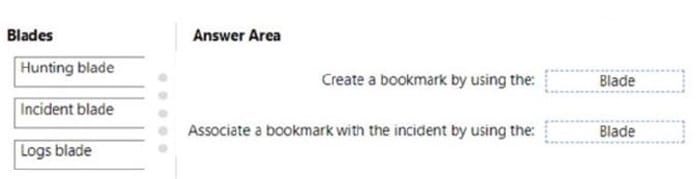
DRAG DROP
You have a Microsoft Sentinel workspace that contains an Azure AD data connector.
You need to associate a bookmark with an Azure AD-related incident.
What should you do? To answer, drag the appropriate blades to the correct tasks. Each blade may be used once, more than once, or not at all. You may need to drag the split bar between panes or scroll to view content
NOTE: Each correct selection is worth one point.
Select and Place:
Questions 6
Your company uses Azure Sentinel to manage alerts from more than 10,000 IoT devices.
A security manager at the company reports that tracking security threats is increasingly difficult due to the large number of incidents.
You need to recommend a solution to provide a custom visualization to simplify the investigation of threats and to infer threats by using machine learning.
What should you include in the recommendation?
A. built-in queries
B. livestream
C. notebooks
D. bookmarks
Questions 7
You provision Azure Sentinel for a new Azure subscription.
You are configuring the Security Events connector.
While creating a new rule from a template in the connector, you decide to generate a new alert for every event.
You create the following rule query.
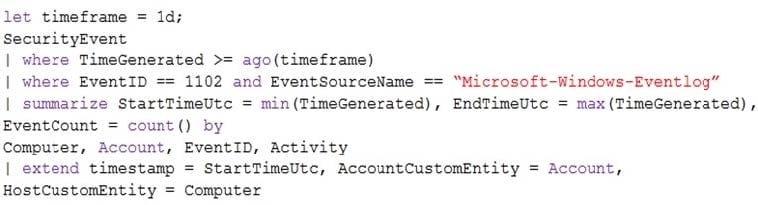
By which two components can you group alerts into incidents? Each correct answer presents a complete solution. NOTE: Each correct selection is worth one point.
A. user
B. resource group
C. IP address
D. computer
Questions 8
You create a custom analytics rule to detect threats in Azure Sentinel.
You discover that the rule fails intermittently.
What are two possible causes of the failures? Each correct answer presents part of the solution.
NOTE: Each correct selection is worth one point.
A. The rule query takes too long to run and times out.
B. The target workspace was deleted.
C. Permissions to the data sources of the rule query were modified.
D. There are connectivity issues between the data sources and Log Analytics
Questions 9
A user wants to sign in from a location which has never been used by the other users in your organization. Which anomaly detection policy will you use if you need to receive a security alert ?
A. Activity from infrequent country
B. Activity from anonymous IP addresses
C. Impossible travel
D. Malware detection
Questions 10
You have a Microsoft 365 subscription that contains 1,000 Windows 10 devices. The devices have Microsoft Office 365 installed. You need to mitigate the following device threats:
1.
Microsoft Excel macros that download scripts from untrusted websites
2.
Users that open executable attachments in Microsoft Outlook
3.
Outlook rules and forms exploits What should you use?
A. Microsoft Defender Antivirus
B. attack surface reduction rules in Microsoft Defender for Endpoint
C. Windows Defender Firewall
D. adaptive application control in Azure Defender
Questions 11
You have an Azure subscription that uses Microsoft Defender for Cloud and contains a resource group named RG1. RG1. You need to configure just in time (JIT) VM access for the virtual machines in RG1. The solution must meet the following
1.
Limit the maximum request time to two hours.
2.
Limit protocol access to Remote Desktop Protocol (RDP) only.
3.
Minimize administrative effort. What should you use?
A. Azure AD Privileged Identity Management (PIM)
B. Azure Policy
C. Azure Front Door
D. Azure Bastion
Questions 12
You have an Azure subscription that uses Microsoft Defender for Cloud. You need to filter the security alerts view to show the following alerts:
1.
Unusual user accessed a key vault
2.
Log on from an unusual location
3.
Impossible travel activity Which severity should you use?
A. Informational
B. Low
C. Medium
D. High
Questions 13
You have an Azure subscription that uses Microsoft Defender for Cloud and contains 100 virtual machines that run Windows Server.
You need to configure Defender for Cloud to collect event data from the virtual machines. The solution must minimize administrative effort and costs.
Which two actions should you perform? Each correct answer presents part of the solution.
NOTE: Each correct selection is worth one point.
A. From the workspace created by Defender for Cloud, set the data collection level to Common.
B. From the Microsoft Endpoint Manager admin center, enable automatic enrollment.
C. From the Azure portal, create an Azure Event Grid subscription.
D. From the workspace created by Defender for Cloud, set the data collection level to All Events.
E. From Defender for Cloud in the Azure portal, enable automatic provisioning for the virtual machines.