SY0-601 Online Practice Questions and Answers
Questions 4
A network engineer and a security engineer are discussing ways to monitor network operations. Which of the following is the BEST method?
A. Disable Telnet and force SSH.
B. Establish a continuous ping.
C. Utilize an agentless monitor
D. Enable SNMPv3 With passwords.
Questions 5
A network engineer is troubleshooting wireless network connectivity issues that were reported by users. The issues are occurring only in the section of the building that is closest to the parking lot. Users are intermittently experiencing slow speeds when accessing websites and are unable to connect to network drives. The issues appear to increase when laptop users return desks after using their devices in other areas of the building. There have also been reports of users being required to enter their credentials on web pages in order to gain access to them.
Which of the following is the MOST likely cause of this issue?
A. An external access point is engaging in an evil-twin attack.
B. The signal on the WAP needs to be increased in that section of the building.
C. The certificates have expired on the devices and need to be reinstalled.
D. The users in that section of the building are on a VLAN that is being blocked by the firewall
Questions 6
A security administrator is compiling information from all devices on the local network in order to gain better visibility into user activities. Which of the following is the best solution to meet this objective?
A. SIEM
B. HIDS
C. CASB
D. EDR
Questions 7
Users are presented with a banner upon each login to a workstation. The banner mentions that users are not entitled to any reasonable expectation of privacy and access is for authorized personnel only. In order to proceed past that banner. users must click the OK button. Which of the following is this an example of?
A. AUP
B. NDA
C. SLA
D. MOU
Questions 8
During a recent security incident at a multinational corporation a security analyst found the following logs for an account called user:
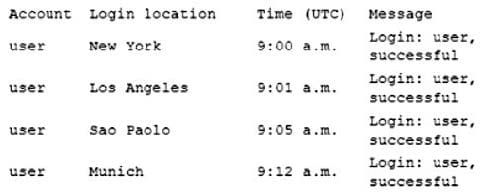
Which of the following account policies would BEST prevent attackers from logging in as user?
A. Impossible travel time
B. Geofencing
C. Time-based logins
D. Geolocation
Questions 9
After a recent security incident, a security analyst discovered that unnecessary ports were open on a firewall policy for a web server. Which of the following firewall policies would be MOST secure for a web server?
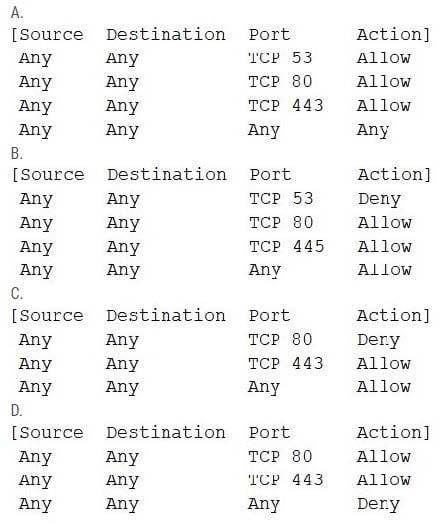
A. Option A
B. Option B
C. Option C
D. Option D
Questions 10
A recent malware outbreak across a subnet included successful rootkit installations on many PCs, ensuring persistence by rendering remediation efforts ineffective. Which of the following would BEST detect the presence of a rootkit in the future?
A. FDE
B. NIDS
C. EDR
D. DLP
Questions 11
A security administrator Is evaluating remote access solutions for employees who are geographically dispersed. Which of the following would provide the MOST secure remote access? (Select TWO).
A. IPSec
B. SFTP
C. SRTP
D. LDAPS
E. S/MIME
F. SSL VPN
Questions 12
A company recently expenenced an attack dunng which #5 main website was directed to the atacker's web server, allowing the attacker to harvest credentials from unsuspecting customers. Which of the following snould the company Implement to prevent this type of attack from accurting in the future?
A. IPSec
B. SSL/TLS
C. DNSSEC
D. S/MIME
Questions 13
A financial analyst has been accused of violating the company's AUP and there is forensic evidence to substantiate the allegation, Which of the following would dispute the analyst's claim of innocence?
A. Legal hold
B. Order of volatility
C. Non-repudiation
D. Chain of custody
