Hacker Tools, Techniques, Exploits and Incident Handling: SEC504
Want to pass your Hacker Tools, Techniques, Exploits and Incident Handling SEC504 exam in the very first attempt? Try Pass2lead! It is equally effective for both starters and IT professionals.
- Vendor: SANS
- Exam Code: SEC504
- Exam Name: Hacker Tools, Techniques, Exploits and Incident Handling
- Certifications: Certified Incident Handler
- Total Questions: 328 Q&As
- Updated on: Apr 16, 2024
- Note: Product instant download. Please sign in and click My account to download your product.

- Q&As Identical to the VCE Product
- Windows, Mac, Linux, Mobile Phone
- Printable PDF without Watermark
- Instant Download Access
- Download Free PDF Demo
- Includes 365 Days of Free Updates
VCE
- Q&As Identical to the PDF Product
- Windows Only
- Simulates a Real Exam Environment
- Review Test History and Performance
- Instant Download Access
- Includes 365 Days of Free Updates
Passing Certification Exams Made Easy
Everything you need prepare and quickly pass the tough certification exams the first time
- 99.5% pass rate
- 7 Years experience
- 7000+ IT Exam Q&As
- 70000+ satisfied customers
- 365 days Free Update
- 3 days of preparation before your test
- 100% Safe shopping experience
- 24/7 Support
SANS SEC504 Last Month Results
Free SEC504 Exam Questions in PDF Format
Related Certified Incident Handler Exams
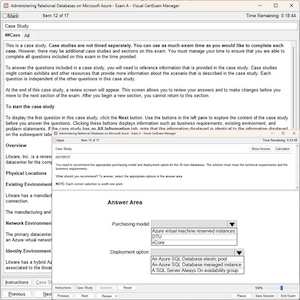
SEC504 Online Practice Questions and Answers
Questions 1
The Klez worm is a mass-mailing worm that exploits a vulnerability to open an executable attachment even in Microsoft Outlook's preview pane. The Klez worm gathers email addresses from the entries of the default Windows Address Book (WAB).
Which of the following registry values can be used to identify this worm?
A. HKEY_LOCAL_MACHINE\Software\Microsoft\Windows\CurrentVersion\RunServices
B. HKEY_LOCAL_MACHINE\Software\Microsoft\Windows\CurrentVersion\Run
C. HKEY_CURRENT_USER\Software\Microsoft\WAB\WAB4\Wab File Name = "file and pathname of the WAB file"
D. HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run
Questions 2
Which of the following are countermeasures to prevent unauthorized database access attacks? Each correct answer represents a complete solution. Choose all that apply.
A. Session encryption
B. Removing all stored procedures
C. Applying strong firewall rules
D. Input sanitization
Questions 3
You want to measure the number of heaps used and overflows occurred at a point in time. Which of the following commands will you run to activate the appropriate monitor?
A. UPDATE DBM CONFIGURATION USING DFT_MON_TABLE
B. UPDATE DBM CONFIGURATION DFT_MON_TIMESTAMP
C. UPDATE DBM CONFIGURATION USING DFT_MON_BUFPOOL
D. UPDATE DBM CONFIGURATION USING DFT_MON_SORT
Reviews
-
Passed with unexpected score. A big surprise. Thanks very much.
-
Thanks for my friend's introduction, I passed the exam by using this study material luckily. Good lucky to you!
-
Update quickly and be rich in content,this dumps is really valid. Thanks.
-
hi guys i had exam yesterday and passed
It is really a good dumps.Thanks very much. -
passed the exam today. all the question from this dumps,so you can trust on it.
-
Thanks for your help I pass my exam. I will be your regular customer and recommend you to all my colleagues.
-
I'm so glad that I have chosen you as my assistant with my exam. I passed my exam. Full scored. I will recommend to friends.
-
A valid dumps. It helped me pass the exam in short time. Thanks a million.
-
Valid dumps, recommend strongly.
-
Passed today with full score. I prepare only with this dumps. Valid.

 Printable PDF
Printable PDF